Novel Sequence Number Based Secure Authentication Scheme for Wireless LANs
2015-11-18RajeevSinghandTeekParvalSharma
Rajeev Singh and Teek Parval Sharma
Novel Sequence Number Based Secure Authentication Scheme for Wireless LANs
Rajeev Singh and Teek Parval Sharma
—Authentication per frame is an implicit necessity for security in wireless local area networks(WLANs). We propose a novel per frame secure authentication scheme which provides authentication to data frames in WLANs. The scheme involves no cryptographic overheads for authentication of frames. It utilizes the sequence number of the frame along with the authentication stream generators for authentication. Hence, it requires no extra bits or messages for the authentication purpose and also no change in the existing frame format is required. The scheme provides authentication by modifying the sequence number of the frame at the sender, and that the modification is verified at the receiver. The modified sequence number is protected by using the XOR operation with a random number selected from the random stream. The authentication is lightweight due to the fact that it requires only trivial arithmetic operations like the subtraction and XOR operation.
Index Terms—Per frame authentication, secure authentication, wireless local area networks, wireless security.
1. Introduction
Authentication is one of the important defenses in the security of a system. In secure wireless local area networks(WLANs) communication, wireless stations (STAs) and an access point (AP) must authenticate each other’s frames. The per frame authentication (of data frames) involved should also satisfy other requirements of a secure communication, such as maintaining secrecy (encryption),integrity (message integrity code (MIC)), and key refreshing. The existing lightweight authentication mechanisms[1]-[7]do not satisfy the requirements of secure communication. They target only authentication leaving other issues like secrecy, integrity, and key refreshing. For authentication, these mechanisms generally use extra bit(s)which increases the communication overhead.
The IEEE 802.11i[8]based networks provides necessary security features like authentication, integrity, and confidentiality while ignoring the availability concerns. This makes it susceptible to the Denial of Service (DoS)attacks[9]-[12]. Per frame authentication (for data frame) is implicitly performed via MIC verification. An attacker may utilize this fact to send large number of frames with wrong MIC, engaging the receiver to verify the MICs. MIC verification involves computation time of the order of 0.75 ms[13],[14]and hence may cause DoS attacks (computation DoS), especially against AP. Above all, the key involved in 802.11i for encryption and MIC evaluation is not refreshed for each frame. But the 4-way handshake (involving four data frames) is required every time to evolve a fresh key. As per the mean time for 4-way handshake in IEEE 802.11i is 16.1 ms which is large enough for refreshing key per frame[15].
In this paper, we intend to separate the authentication and cryptographic functionality (MIC and encryption/ decryption) in the data frames. This helps in protection against computation DoS attacks. Here, the data frame itself provides implicit authentication via its sequence number. The authentication is lightweight due to the fact that it requires only trivial arithmetic operations like subtraction and XOR operation. No extra messages or bits per frame are required for authentication, which minimizes the communication overhead. As the scheme does not allow revealing the shared seed values and sequence numbers, it provides a secure authentication mechanism. The scheme prohibits, replays, and maintains the synchronization in case of loss of frames. Thus, the main contribution of the paper is utilization of the sequence number for authentication of data frames in a secure manner.
The rest of the paper is arranged as follows. Section 2 provides a brief review of the existing solutions that provide per frame authentication in WLANs. Section 3 presents the proposed sequence number based secure authentication scheme along with the property comparisons. Section 4 provides the performance and security analysis. Section 5 draws conclusions.
2. Related Work
Researchers have proposed several lightweight per frame authentication schemes[1]-[7]for WLANs. The statistical one bit lightweight authentication protocol(SOLA)[1]provides one bit identity authentication per frame to the authorized communicating party (one with the shared secret key). The use of single bit greatly reduces the communication overhead. SOLA[1]generates the authentication stream based upon the key shared between the communicating parties. The protocol requires one additional bit to be placed in the medium access control(MAC) or Internet protocol (IP) header and one bit indicating the success or failure in the returned acknowledge (ACK) frame. SOLA is vulnerable to DoS attacks and guessing of the identity authentication bit attack(attacker’s chances to guess a single bit are quite high(50%)). To detect these attacks, a failure threshold is kept. A failure threshold value greater than 50% indicates attacks,which calls for resetting the authentication. The synchronization scheme involves increasing the authentication bit stream of both of the sender and receiver to the next opposite bit plus 1 in case of non synchronization. Wang et al. also proposed a one bit lightweight protocol for access control in 802.11 networks[2]. The protocol provides continuous authentication, which is suitable for high mobility wireless networks as the overhead of authentication is little (single bit is used for authentication). In case of non synchronization detected, it takes less time to stabilize, as resynchronization is done only by the sender in its authentication bit stream. The attacker may utilize this fact and can modify or replay the receiver’s response to confuse the sender. This may lead the sender to resynchronize unnecessarily, in the worst case the sender may become busy most of the time. The system also cannot differentiate between the instances when the system is in non synchronization due to the packet loss or due to the attacker utilizing a long authentication stream of 0 or 1. Wang et al. later improvised the synchronization algorithm and came with 3 approaches[3]. These approaches deal with the pointer movement in the authentication bit streams. It also finds statistically the authenticity of the mobile node. These protocols provide only authentication but do not talk about the confidentiality (packet encryption), integrity, and key management. The number of synchronization run in both [2]and [3] varied in accordance to the difference of the distance between the communicating parties’ authentication bit strings. The performances of these schemes decrease with the increase in the number of synchronization runs. It is also possible that the authentication bit stream may lose synchronization itself[4]. An enhancement to Wang’s scheme was done by Ren et al.[4]. It provides a higher probability for attack detection by utilizing more bits (3 bits)for authentication at the MAC layer. It is compatible with the existing frame structure of WLANs. The scheme only detects the attacks by using a statistical method but does not provide any confidentiality, integrity, and key management. For these issues it depends upon higher layer measures (like the Internet protocol security (IPsec) at the network layer). The major drawback in it is the fact that it does not authenticate the ACK frames. An attacker with the false synchronization information (wrong value of counter) in ACK failure can easily fool the sender. The chances that the sender and receiver are non-synchronized and still the 3 bit authentication bits (stuffed by the attacker) are matched are 8-1(0.125). Lee et al. also proposed similar random bit authentication. It considers protection only against DoS attacks conducted via management frames[5]. Out of 8 spoofed packets, the success rate of attacker is again 8-1(0.125).
The synchronized pseudo random number generation(SPRiNG)[6]is a symmetric key authentication protocol which tries to prevent the replay attacks and avoid key reuse. Both the sender and receiver are synchronized and generate their pseudo random numbers which are used as authenticator variables. These are also utilized as the unique encryption key for each data frame. The SPRiNG synchronization process is prone to DoS attacks. Sufficient number of authentication errors may result in session termination, re-association, and re-establishment of the synchronization counters. DoS can even be conducted by changing the counter values such that it becomes different from that of the receiver. Pseudo random numbers generated in the scheme depend only upon the previous pseudo random number. This can compromise the entire sequence generated hence after. Lee et al. proposed a puzzle based WLAN authentication solution[7]. However, it does not provide frame level authentication of data frames and is prone to DoS attacks. Aslam et al. provided a pseudo randomized sequence number based solution but this pertains only to dissociation frames[16].
The lightweight authentication schemes discussed, raise the issue of synchronization which is important in the WLANs as packets might get lost or be tampered frequently. The attacker chances are also quite high in these schemes as few number of bits are involved in authentication. Most importantly, most of these do not involve the encryption or protection of the authentication bit streams or data packets. Thus, none of these schemes provide a secure authentication solution. So we propose a per frame secure authentication scheme, which provides secure frame level authentication to data frames.
3. Proposed Sequence Number Based Secure Authentication Scheme
The proposed authentication scheme is based upon the generation and verification of authentication sequencenumbers (ASNs) by the sender and receiver. The ASN is derived from the sequence number (inserted in the sequence control field of the frame). The sequence control field (as shown in Fig. 1) is a 16-bit sequence number used to provide sequence control of the frames, i.e., a 12-bit sequence number of the MAC service data unit (MSDU)plus a 4-bit fragment number is used to identify and order the fragments. In the lightweight authentication schemes[1]-[7], the sequence numbers are not fitted for the synchronization purpose as in case of frame retransmission sequence numbers remains the same and do not contribute to any advancement of the authentication stream. Moreover,sequence numbers repeat after some time due to overflow and are sent in clear, they do not meet the intended authentication purpose. In the proposed scheme we assume,the sender and receiver start from a commonly shared sequence number that can start from any chosen value. This sequence number is stored along with the keying material both on the sender and receiver. Thus, AP maintains sequence numbers per STA.
3.1 Authentication Sequence Number Generation
The entire process of authentication is shown in Fig. 2. The sender and receiver both share three seed values for the generation of three authentication streams by using the authentication stream generator (ASG). We assume the existence of Diffie-hellman key exchange algorithm for deriving the shared common key. For sharing the seeds, the encryption using the commonly derived Diffie-hellman key is utilized. In case the stronger authentication is required,the 802.1X[17]based or client puzzle based[10]algorithms can be used for initial authentication.
The authentication streams are numbered as AS1, AS2,and AS3. The sender selects three bits from the first stream(AS1) each time when a new frame is to be sent. Based upon its numeric value (in decimal), the bits from the second bit stream (AS2) are simultaneously selected. The numeric value (in decimal) of these bits is subtracted from the sequence number. We term the value that is obtained after subtracting as the subtracted sequence number. Sixteen bits are now selected from the third stream (AS3)and XORed with the subtracted sequence number. The number obtained hence is termed as the authentication sequence number (ASN). Thus, the third stream is used for providing protection to the subtracted sequence number. The protected authentication sequence number is sent to the receiver to provide per frame authentication. It is sent in the sequence number field of the 802.11 frame header and hence, does not require extra bits or frames for the authentication purpose. The verification of the authentication sequence number by the receiver results in the authentication of the sender for each frame.

Fig. 1. 802.11 MAC frame format.

Fig. 2. Proposed sequence number based per frame authentication scheme.
In Fig. 2, the frame sequence number for frame1 is 2358. The sender selects 3 bits (the value equals 5) from AS1 and then selects 5 bits from AS2 (the value equals 26). It thus,subtracts 26 from the sequence number giving 2332 which is XORed with the 16 bit value selected from AS3 (3414) to give the authentication sequence number as 1098. Hence,the sender puts 1098 in the sequence control field of the frame header and sends the frame.
For ACK, the sequence number is 2359. The sender selects 3 bits (the value is equal to 6) from AS1 and then selects 6 bits from AS2 (the value is equal to 61). It thus,subtracts 61 from the sequence number resulting in 2298 which is XORed with the 16 bit value selected from AS3(3550) to give the authentication sequence number as 1316. Hence, 1316 is put in the sequence control field of the frame header. Similarly, ASN for the next data frame is calculated (as 2796). The strength of the scheme lies in the fact that any two authentication sequence numbers (here,1098, 1316, and 2796) are not related with each other while hiding the original sequence numbers (here, 2358, 2359,and 2360) of the frames.
3.2 Verification at the Receiver
On receipt of a frame, the receiver generates the authentication sequence number. The receiver matches the generated and received authentication sequence numbers to authenticate the sender. Upon authentication, the message integrity code (MIC) is checked. After its successful verification, the receiver decrypts the frame (if it is encrypted) and returns the ACK with the next ASN. Thus,the ACK is also protected and authenticated, which makes the scheme robust against attacks that are targeted against the ACK.
For the case of bulk transfer, i.e. more than one frame transfers in a time interval by the sender, we assume that the upper limit on the number of frames to be transmitted in bulk in a session is negotiated at the time of association. The receiver counts the number of such frames received within a fixed time interval. It then calculates the equal number of authentication sequence numbers. Now instead of matching with one, the receiver has to match with all the authentication sequence numbers of frames received in bulk. After the verification of all the frames, ACK is returned with the current ASN. The frames of the attacker will fail in verification and are hence dropped.
3.3 Synchronization Issues
No synchronization is required under the single frame transfer case, as the next frame is transferred only after the receipt of the ACK. Synchronization is required under bulk frame transfer. The sender and receiver may lose synchronization due to the loss of data frames or due to the loss of ACK frames. In case of losing data frames, the receiver sends the ACK with ASN (corresponding to the latest sequence number till where frames were received properly) and supporting ASN. The ASN will obviously be a repeated one and it indicates the data frame loss to the sender. The receiver selects a random number (rn), adds it to the numeric value of AS2 in the calculation, and obtains corresponding ASN (supporting ASN). The selected random number (16 bits) is also sent in the ACK. On noticing the duplicate ASN in the ACK, the sender authenticates the receiver via verifying the supporting ASN. For frame retransmission, the sender selects a random number (rs). The sender adds this number to AS2 and then calculates the ASNs for the retransmission of the frames. The newly calculated ASN and rsare sent in the corresponding data frame to the receiver. On receipt, the receiver verifies the ASN with the help of rs.
If the ACK frame is itself lost, the sender sends the frames again by shifting the pointer in the authentication stream to the place where the last ACK was received correctly. As all the data frames were previously received correctly at the receiver, the receiver sends the previous ACK (lost ACK) with ASN again, ensuring the lost synchronization. Thus, for synchronizing the bulk transfer,buffering of frames and corresponding ASNs at the sender and receiver are required.
3.4 Security Issues
The encryption of the data frames is done by using the existing secure symmetric key mechanisms like the temporal key integrity protocol (TKIP) or the advanced encryption standard (AES) in the counter mode. The current sequence number is XORed with the key and the resultant is used as the encryption key. As the current sequence number is increased for each frame, the encryption key is refreshed for each frame. For maintaining MIC, AES in the cipher block chaining message authentication code (CBC-MAC) protocol (CCMP) is utilized. MIC is evaluated by using the newly refreshed key. The refreshed key in the proposed scheme is neither exposed nor vulnerable to the attacks.
3.5 Implementation Issues
The authentication sequence numbers are put in the sequence control field of the MAC header. This prevents the use of extra bits or frames for the authentication purpose and hence makes the scheme lightweight in terms of communication overhead. The data is sent and encrypted in the frame body as payload. It is encrypted by using the refreshed key. The ASN, supporting ASN, and selected random number are added in the MAC header of the ACK frame. This helps the two communication parties under non-synchronization to synchronize. This overhead (48 bits)is justified, as the ACK frame has a small size. If thefragmentation is used then, all calculations pertaining to ASN will be performed by using 12 bits only (i.e. the size of the sequence numbers and the size of AS3 will be equal to 12 bits in this case) and the remaining 4 bits of the sequence control field will indicate the fragment number. In the current work, we consider ASN in the size of 16 bits.
3.6 Feature Comparison with Related Solutions
Feature comparisons of the proposed scheme with per frame authentication solutions and related security protocols are shown in Table 1. The proposed scheme provides strong and continuous authentication. It involves initial message exchanges for key exchange and seed sharing. It also enjoys high confidentiality based upon existing symmetric encryption mechanisms. The message integrity is maintained by using MIC. The scheme provide secure authentication and has the synchronization mechanism. It also maintains key freshness per frame without exchanging any extra messages.

Table 1: Feature comparisons of the proposed scheme with per frame authentication solutions and related security protocols
4. Analysis of Proposed Scheme
The proposed scheme is a secure authentication scheme which provides per frame authentication and does not use any third party like authentication server (AS) in the authentication process. The security of the scheme lies in the security of the seed values and sequence number. The ACK frames are also protected and authenticated, which provides extra strength to the scheme. It is difficult to provide the authentication to management frames before the shared key is exchanged. But once the key is exchanged,the proposed ASN method can also be utilized to provide authentication to management frames. MIC calculations,data encryption, and key refreshing are ignored for management frames.
4.1 Performance Analysis
The proposed scheme requires memories for storing the seeds, sequence number, shared key, and authentication stream. In case of bulk transfer, the storage of the frames along with ASNs is also required. Thus, the scheme has nominal memory requirements. The scheme has no extra communication overhead (Table 2) during authentication as no extra bits and frames are involved. And 48 bits per ACK frame are required for synchronization purpose.
For calculating the computation overhead, let TKeyrefresh,TEnc, TIntegrity, TASG, and TRandombe the time complexity for key refreshing, encryption/decryption, integrity (CRC/MIC),authentication stream generation, and random number generation, respectively. Typically, time complexity associated with these operations can be roughly expressed as TASG<TRandom<TKeyrefresh<TIntegrityand TEnc. Our scheme requires computations for encryption/decryption (TEnc),finding MIC (TIntegrity), and generating authentication sequence number (TASG). It is obvious that the computational performance of the first five authentication schemes[1]-[5]is better than the remaining schemes in Table 2. This is due to the fact that no MIC is used and no encryption is performed in these schemes. The encryption and MIC provide security features and hence extra computations in our scheme are justified. If we compare only the computational cost for authentication, we find that our scheme performance is equivalent to others. For finding the computational cost for authentication, we recorded the time by using a C program to generate authentication sequence number on a machine running under Ubuntu with a core2duo processor (2.66 GHz) and 1 GB RAM. The time taken is of the order of 0.5 ms. This justifies that it is lightweight authentication.
4.2 Security Analysis
Comparisons of existing approaches with our scheme from the perspective of security properties, like brute force attacks, modification, man-in-middle, replay, and availability (DoS), are given in Table 3. The comparisons clearly indicate that the proposed scheme provides the security almost equivalent to 802.11i. The security of the scheme lies in the fact that it is difficult to guess and calculate the sequence numbers used during the authentication. For finding the sequence number, the attacker will have to first decode the communicated authentication sequence number. For decoding, the attacker must know the corresponding AS1, AS2, and AS3 values.The attacker does not have seed values, so he cannot evaluate AS1, AS2 and AS3 values. He can apply the brute force method for finding the ASN. The probability of guessing all 16 bits correctly is 2-16, i.e. 0.000015. And this will only lead to authentication of one frame only and do not affect the entire scheme.
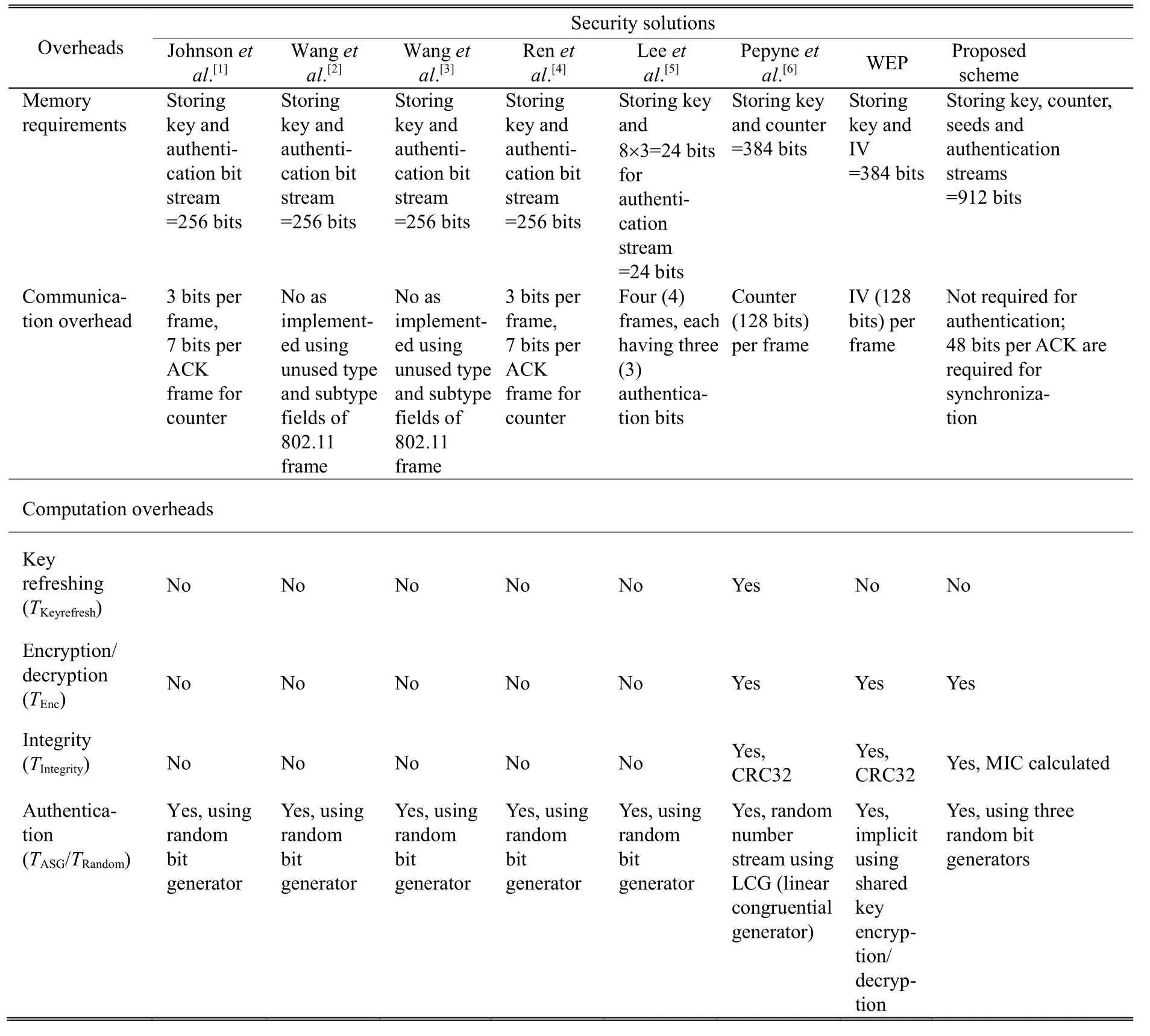
Table 2: Performance comparison of our scheme with other security solutions
Message modification or insertion attacks are not possible due to the fact that the ASN cannot be generated by the attacker as he lacks the necessary information for it. MIC of the message is evaluated by using the sequence number (refreshed key). This binds the message and the authentication sequence number since which message modification or insertion is not possible.
Man-in-middle attacks are impossibilities as the attacker does not have the access to the seed values and sequence number. Moreover, the message is protected by using encryption and MIC. Replay attacks cannot be carried out as the scheme is robust under the duplicate frame and replayed frames. A data frame with unknown ASN or a frame with duplicate ASN is silently dropped at the receiver. Thus, the acceptance of the replayed frame that is already authenticated previously is not possible here as such frame will be discarded immediately at the receiver due to the failure of authentication sequence number verification.
DoS attacks are impossible as every frame including the ACK frame is authenticated. The attacker frames lack the ASN and hence are dropped at the receiver. The DoS attack conducted via wrong MIC is not effective as the scheme separates the authentication from the integrity check. CPU exhaustion is not necessary to consider as the verification of the ASN takes very less time. We recorded the time using a C program to generate the authentication sequence number on a machine running under Ubuntu with a core2duo processor (2.66 GHz) and 1 GB RAM. It is of the order of 0.5 ms. For conducting a DoS attack against such a machine, an attacker needs to keep the processor busy all the time. For conducting an attack for one second,an attacker needs to send at least 2 million frames(1/(0.5×10-6)=2×106) per second. An attacker machine flooding at such a high rate can easily be identified and necessary actions can be taken.
Also as memories occupied by ASN are not large, no memory exhaustion DoS is possible. For the case of bulk transfer, frames that fail to match the calculated authentication sequence numbers are dropped by default,preventing the attack. Thus, the DoS attack is made ineffective by the proposed authentication scheme.
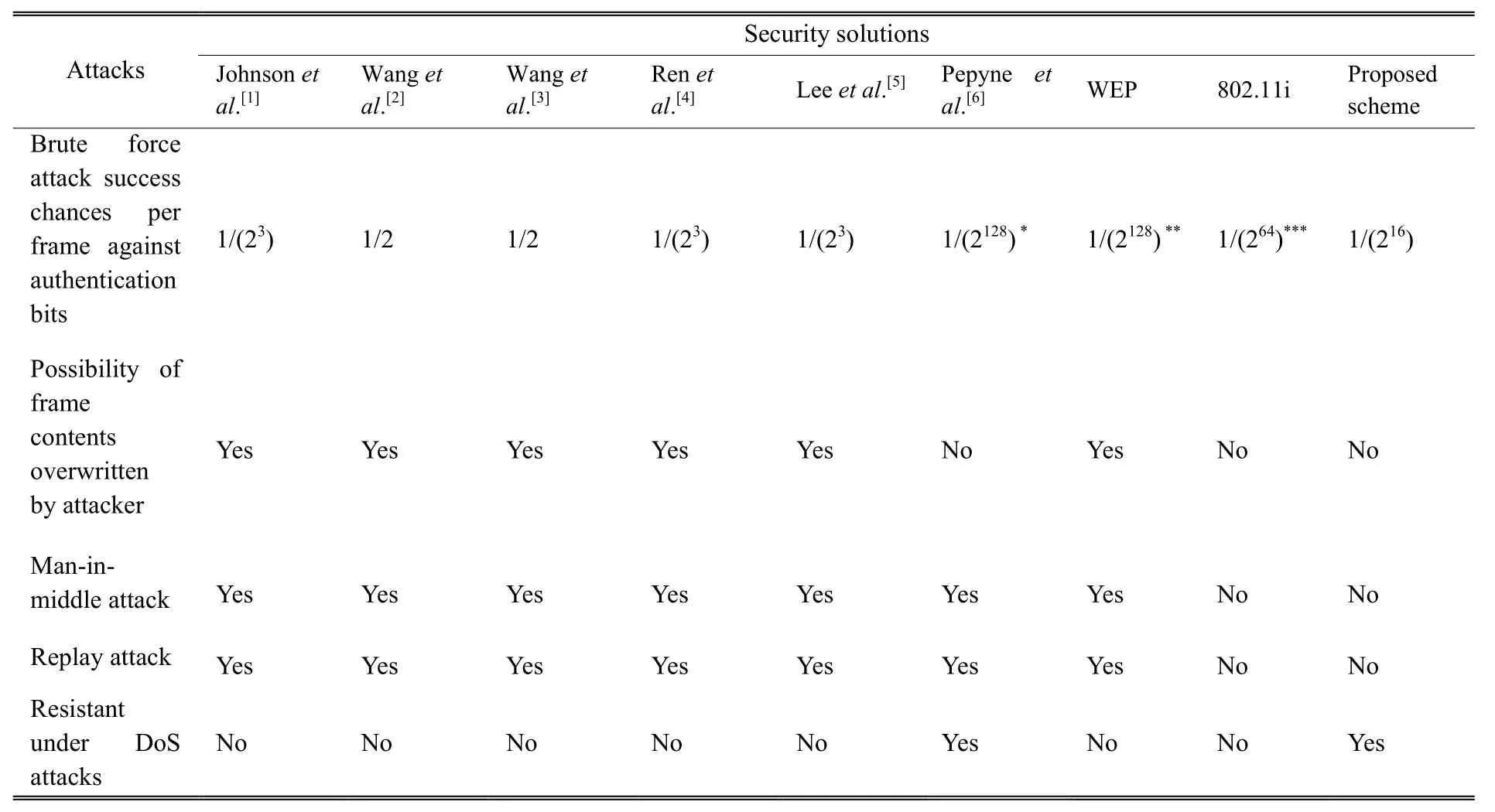
Table 3: Comparison of our scheme with other security solutions under attacks
The proposed scheme satisfies an important security property that the two authentication sequence numbers are not related with each other, i.e., the frames with the same sequence number and different authentication sequence numbers are obtained. For example, if the frames have the same sequence number (this possibility increases when the sequence numbers overflow and rotate through the same value) then the 3 bit values selected from AS1 may be different, leading to the selection of different numbers of bits and hence, different values from AS2. Also the 16 bit sequence taken from AS3 will be different. Thus, no correlation between any two authentication sequencenumbers is obtained, i.e., they are not related in any sense with each other.
Assuming the number of bits selected from ASG2, d, is 3, then the probability that the same authentication sequence number is generated by our scheme is equal to
(Probability that same sequence number is selected)×(Probability that same value from ASG1 is selected)×(Probability that same value from ASG2 is selected)×(Probability that same value from ASG3 is selected)
=(1/216)×(1/23)×(1/2d)×(1/216)
=1/238
=3.638×10-12
which is too low in view of the fact that it is per frame authentication. In other words, this means that the possibility that the same authentication sequence number will be generated is one out of 274877906944. Thus, it is justified to consider that a unique authentication sequence number can be generated for each sequence number.
The length of bits selected from AS2 is varied so that the person who gains the access to seed2 is still unable to find the value of the number selected for the subtraction purpose. Thus a person requires both the seed values for cracking the entire authentication mechanism. And eavesdropping is not possible as the frames are encrypted by using the refreshed key. The attack by malicious AP is not effective as malicious AP lacks the authentication sequence numbers.
5. Conclusions
We propose a symmetric key based secure WLAN communication scheme. The scheme utilizes a sequence number based authentication method to provide security per frame. To show the effectiveness of the scheme, we provide the property comparisons, performance analysis, and security analysis between the proposed scheme and the existing related WLAN authentication solutions. The performance analysis shows that our scheme is efficient in authentication, and the security analysis shows that it enjoys almost equivalent security as compared with 802.11i. In comparisons with other per frame and related authentication solutions, it is equivalently efficient and enjoys more security.
[1] H. Johnson, A. Nilsson, J. Fu, S.-F. Wu, A. Chen, and H. Huang, “SOLA: A one bit identity authentication protocol for access control in IEEE 802.11,” in Proc. of IEEE Global Telecommns Conf., 2002, pp. 768-772.
[2] H. Wang, A. Velayutham, and Y. Guan, “A lightweight authentication protocol for access control in IEEE 802.11,”in Proc. of IEEE Global Telecommns Conf., 2003, pp. 1384-1388.
[3] H. Wang, J. Cardo, and Y. Guan, “Shepherd: A lightweight statistical authentication protocol for access control in wireless LANs,” Computer Communications, vol. 28, no. 14,pp. 1618-1630, 2005.
[4] K. Ren, H. Lee, J. Park, and K. Kim, “An enhanced lightweight authentication protocol for access control in wireless LANs,” in Proc. of the 4th Int. Conf. on Networks,Daejeon, 2004, pp. 444-450.
[5] Y-S. Lee, H-T. Chien, and W-N. Tsai, “Using random bit authentication to defend IEEE 802.11 DoS attacks,” Journal of Information Science and Engineering, vol. 25, no. 5, pp. 1485-1500, 2009.
[6] D. L. Pepyne, Y. C. Ho, and Q. Zheng, “SPRiNG: synchronized random numbers for wireless security,” in Proc. of IEEE Wireless Communications and Networking,2003, pp. 2027-2032.
[7] I. Lee and R. Hunt, “A novel design and implementation of Dos resistant authentication and seamless handoff scheme for enterprise WLANs,” in Proc. of Australian Information Secuity Management, Perth, 2010, pp. 49-61.
[8] IEEE 802.11i, Wireless LAN Medium Access Control (MAC)and Physical Layer (PHY) Specifications: Medium Access Control (MAC) Security Enhancements, IEEE Standard,2004.
[9] C. He and J. C. Mitchell, “Security analysis and improvements for IEEE 802.11i,” in Proc. of the Annual Network and Distributed System Security Symposium, 2005,pp. 90-110.
[10] C. S. Park, “Two-way handshake protocol for improved security in IEEE 802.11 wireless LANs,” Elseνier Journal Computer Communications, vol. 33, no. 9, pp. 1133-1140,2010.
[11] F. D. Rango, D. C. Lentini, and S. Marano, “Static and dynamic 4-Way handshake solutions to avoid denial of service attack in Wi-Fi protected access and IEEE 802.11i,”Journal on Wireless Communication and Network,doi:10.1155/WCN/2006/47453
[12] L. Wang and B. Srinivasan, “Analysis and improvements over DoS attacks against IEEE 802.11i standard,” in Proc. of IEEE Int. Conf. on Network Security, Wireless Communications, and Trusted Computing, 2010, pp. 109-113.
[13] I. Martinovic, F. A. Zdarsky, A. Bachorek, and J. B. Schmitt,“Measurement and analysis of handover latencies in IEEE 802.11i secured networks,” in Proc. of the European Wireless Conf., Paris, 2007, pp. 1-7.
[14] I. Martinovic, F. A. Zdarsky, A. Bachorek, and J. B. Schmitt,Introduction of IEEE 802.11i and Measuring its Security νs. Performance Tradeoff Technical Report 351/06, University of Kaiserslautern, 2006.
[15] I. Martinovic, F. A. Zdarsky, and J. B. Schmitt, “On the way to IEEE 802.11 DoS resilience,” in Proc. of IFIP Networking 2006, Workshop on Security and Priνacy inMobile and Wireless Networking, Coimbra, 2006, pp. 1-15.
[16] B. Aslam, M. H. Islam, and S. A. Khan. “Pseudo randomized sequence number based solution to 802.11 disassociation denial of service attack,” in Proc. of Mobile Computing and Wireless Communication Int. Conf., Amman,2006, pp. 215-220.
[17] IEEE Standard for Local and Metropolitan Area Networks—Port-Based Network Access Control, IEEE Standard 802.1X-2001.

Rajeev Singh received his M.Tech. degree in computer science & engineering from Indian Institute of Technology, Roorkee, India in 2008 and his Ph.D. degree from National Institute of Technology, Hamirpur, India in 2014. Currently, he is working as an assistant professor with the Department of Computer Engineering, Govind Ballabh Pant University of Agriculture & Technology, Uttarakhand, India. His research interest includes computer networks and network security.

Teek Parval Sharma received his Ph.D degree from Indian Institute of Technology,Roorkee, India in 2009 in the area of wireless sensor networks. He is an associate professor with the National Institute of Technology,Hamirpur, India. He has published numerous high quality research papers in international/ national journals and conferences, and has also contributed in various books of international publishers. His research interest includes distributed systems, wireless sensor networks, mobile Ad hoc networks, and wireless networks.
Manuscript received June 25, 2014; revised March 7, 2015.
R. Singh is with the Department of Computer Engineering, Govind Ballabh Pant University of Agriculture & Technology, Pantnagar 263145,India (Corresponding author e-mail: rajeevpec@gmail.com).
T. P. Singh is with the Department of Computer Science and Engineering, National Institute of Technology, Hamirpur 177005, India(e-mail: teekparval@gmail.com).
Digital Object Identifier: 10.3969/j.issn.1674-862X.2015.02.011
杂志排行
Journal of Electronic Science and Technology的其它文章
- QCM Sensors Based on PEI Films for CO2Detection
- Energy-Based Collaborative Spectrum Sensing for Cognitive UWB Impulse Radio
- Monitoring of PON System Using Compound Surveillance Technique
- Design and Realization of an NFC-Driven Smart Home System to Support Intruder Detection and Social Network Integration
- Modeling of a Planar Nine-Way Metamaterial Power Divider/Combiner
- Robust Stability of a Class of Fractional Order Hopfield Neural Networks