Secure Downlink Transmission Strategies against Active Eavesdropping in NOMA Systems:A Zero-Sum Game Approach
2023-02-17YanqiuChenandXiaopengJi
Yanqiu Chen and Xiaopeng Ji
School of Electronics and Information Engineering,Nanjing University of Information Science and Technology,Nanjing,210044,China
ABSTRACT Non-orthogonal multiple access technology(NOMA),as a potentially promising technology in the 5G/B5G era,suffers from ubiquitous security threats due to the broadcast nature of the wireless medium.In this paper,we focus on artificial-signal-assisted and relay-assisted secure downlink transmission schemes against external eavesdropping in the context of physical layer security,respectively.To characterize the non-cooperative confrontation around the secrecy rate between the legitimate communication party and the eavesdropper,their interactions are modeled as a two-person zero-sum game.The existence of the Nash equilibrium of the proposed game models is proved,and the pure strategy Nash equilibrium and mixed-strategy Nash equilibrium profiles in the two schemes are solved and analyzed,respectively.The numerical simulations are conducted to validate the analytical results,and show that the two schemes improve the secrecy rate and further enhance the physical layer security performance of NOMA systems.
KEYWORDS Non-orthogonal multiple access technology(NOMA);physical layer security;game theory;nash equilibrium;zerosum game
1 Introduction
Non-orthogonal multiple access (NOMA) has been envisioned as a potentially promising technology for fifth generation (5G) and beyond 5G (B5G) wireless communication networks for its superior performance over the conventional orthogonal multiple access(OMA)in terms of spectral efficiency,connection density,as well as user fairness[1-4].However,due to the broadcast nature of wireless communication, the NOMA system is vulnerable to eavesdropping. To secure information transmission against malicious eavesdropping, many countermeasures, such as encryption-based approaches implemented at the higher layers [5] and physical layer security (PLS) [6,7], have been put forward in recent years. PLS, as a promising solution to safeguard confidential transmission from the wireless information-theoretic perspective,exploits the intrinsic randomness of the wireless medium to enhance security, and can provide a secure transmission without keys or sophisticated encryption/decryption algorithms. In addition, the physical layer security techniques can be easily implemented and have the capability to quickly adapt to different wireless scenarios[8].
Recently, the concept of PLS has been applied to NOMA systems for secure transmission, and has attracted significant attention and increasing interest in both academia and industry[9,10].The existing work generally falls into two categories:the security-oriented system design,and X-assisted security scheme. Specifically, the security-oriented system design approaches enhance security by optimizing the parameters of the NOMA system,such as beamforming matrix and power allocation coefficients. Whilst, in X-assisted security schemes, X denotes artificial signal, relay, cooperative jamming or something additional.The key idea behind the approaches is to deliberately improve the legitimated communication channel and/or degrade the eavesdropping channel.
Nevertheless,most of the existing studies on secure transmission in NOMA are conducted from the perspective of legitimate communicators,and fail to reflect the confrontation relationship between eavesdroppers and legitimate communicators.In other words,they assume the precondition that the eavesdropper keeps wiretapping regardless of the radio environment.As a matter of fact,eavesdroppers may incur more costs than benefits when faced with harsh eavesdropping channel conditions,and have no intent to eavesdrop in this situation,which makes the precondition more conservative.Therefore,it is of great significance to comprehensively study the interaction strategies between the two sides considering the channel conditions. However, the various and variable channel state information in radio environment complicates the dynamic secure transmission and eavesdropping process, and further affects their optimal strategy selection for both sides,which poses a huge challenge to studying the secure transmission in NOMA system from the interaction perspective.
Fortunately,game theory,as a mathematical theory and tool to study competitive or cooperative behaviors,provides a powerful framework with which the optimal strategies for both/all sides under various solution concepts of equilibrium can be found.In the secure transmission strategy selections of NOMA systems,we study the interaction between the legitimate communicators and the eavesdropper based on game theory.Specifically,both sides will pay the cost and receive the corresponding benefits in the light of the strategy profile comprised of strategies they select,respectively.That is to say,one’s gain is influenced not only by his/her strategy, but also by the other’s. The advantage of doing so is that the optimal secure transmission strategy can be selected by analyzing the opponent’s strategy,and its conservativeness can be reduced to some extent.
Motivated by this, for a NOMA system with external eavesdroppers, we focus on two typical security schemes,artificial-signal-assisted scheme(AS scheme)and relay-station-assisted scheme(RS scheme). Specifically, artificial signals are superimposed in the orthogonal subspace of weak users’transmission directions in AS scheme and relays are employed in weak users’transmission links in RS scheme,to impair the eavesdropping capability.In both schemes,the external active eavesdropper can impose interference signals while eavesdropping to reduce the quality of legitimate communication.In this paper,we first establish the system models,including channel models and signal models,and formulate the information transmission rate for each legitimate communicator and eavesdropper in AS and RS schemes, respectively. Then, the interactions around secure transmission rate, i.e.,secrecy rate,are modeled as two-person zero-sum security games.For each security game model,the existence of Nash equilibrium is proved,and the pure strategy Nash equilibrium and mixed-strategy the Nash equilibrium profile are solved and analyzed. Finally, numerical simulations are conducted to validate the theoretical results,and show that AS and RS schemes can improve the secrecy rate and further enhance the physical layer security performance of NOMA systems. By analyzing the Nash equilibrium of the proposed game model, we can shed some light on the decision-making motives,which is of great significance in the design of security schemes.
The main contributions of this paper can be summarized as follows:
• We are the first to investigate artificial-signal-assisted and relay-station-assisted secure downlink transmission schemes for NOMA systems against external active eavesdropping within the framework of game theory, which integrates eavesdropper’s strategy in the design of secure transmission scheme,improves secrecy rate and further enhances physical layer security performance accordingly.
• We model the confrontational interaction between them as a two-person zero-sum game with secrecy rate as utilities to characterize the impact mechanism of legitimate communicators and active eavesdropper’s strategies on the security performance of the Nash system, prove the existence of the Nash equilibrium, and give the optimal (equilibrium) strategy profile which sheds some light on the design of secure NOMA downlink transmission.
• Through numerical simulations, we demonstrate that legitimate communicators can improve the security performance in terms of secrecy rate by with the help of artificial signals or relay stations, while the active eavesdropper choose to eavesdrop and impose interference signal simultaneously in AS scheme and only eavesdrop in RS scheme.
The rest of the paper is organized as follows. In Section 2, a detailed literature survey of physical layer security issues in NOMA system are discussed.Section 3 describes the system model,including channel model and signal model, in artificial-signal-assisted scheme and relay-assisted scheme,respectively.In Section 4,the interactions between the utility of the legitimate communication party and eavesdropper are modeled as two-person zero-sum game,the utilities are expressed in terms of secrecy rate, the existence of the Nash equilibrium of the proposed game models is proved, and the pure strategy the Nash equilibrium and the mixed-strategy Nash equilibrium profiles are solved and analyzed respectively.In Section 5,the proposed game models are evaluated and verified through numerical simulations.Finally,a conclusion is given in Section 6.
2 Related Works
In the pioneering works on secure communication in NOMA system from the perspective of physical layer security,existing studies in this field can be classified into two categories:the securityoriented system optimization and X-assisted security scheme.In this section,we introduce the security solutions for NOMA communication systems according to the above taxonomy.
2.1 Security-Oriented NOMA System Design
Security-oriented NOMA system design aims to achieve better security performance by optimizing the NOMA communication system in normal operation mode,such as beamforming,power allocation, user pairing, etc. In [11], the authors investigated the physical layer security problem of mm-Wave NOMA network,proposed an analysis framework of security outage probability,develop a minimal angle-difference user pairing scheme and two maximum ratio transmission beamforming schemes to further enhance the secrecy performance.The authors of[12]considered the application of NOMA to a multi-user network with mixed multicasting and unicasting traffic and proposed a design of beamforming and power allocation ensures that the unicasting performance is improved and maintaining the reception reliability of multicasting.In[13],a low-complexity subcarrier assignment scheme was proposed to maximize the achievable secrecy energy efficiency. In [14], the authors investigated the reliable and secure transmission problem of NOMA systems with untrusted near users,and proposed a joint beamforming and power allocation scheme to achieve reliable and secure transmission. The authors of [15] designed a secure transmission scheme based on beamforming optimization to guard against both internal and external eavesdropping of downlink MISO NOMA networks. In [16], the authors considered the PLS against internal eavesdropping and gave the beamforming design and optimal power allocation problems to guarantee the positive secrecy rate of the system.
2.2 X-Assisted Security Solution
Different from security-oriented NOMA system design, X-assisted security solution enhance security by utilizing external “X”, such as artificial signals, relays, etc. We mainly introduce the two mainstream techniques, artificial-signal (AS) and relay-station (RS)-assisted security solutions,respectively.
2.2.1 AS-Assisted Security Solution
The authors of [17] proposed the method of combining weak user information bearing signal and artificial signal in NOMA system to improve the security performance of the system. The security outage performance of artificial noise assisted full duplex downlink NOMA transmission in large-scale networks was investigated in[18].In[19],the authors proposed a new hierarchical PLS model to ensure the security of the transmitted information.And an auxiliary optimal beamforming scheme was proposed to ensure the layered information security. In [20], a new frequency domain artificial noise assisted transmission strategy was proposed to improve the physical layer security of the information receiver and satisfied the energy acquisition requirements of the energy receiver.The authors investigated the problem for the design of artificial noise assisted beamforming in MISO channels from the perspective of security outage. The optimal structure was found by solving the security rate maximization problem constrained by the security outage in[21].
2.2.2 RS-Assisted Security Solution
In [22], the security communication problem in multi hop relay systems was considered, the authors proposed to use full duplex relay to enhance the security of the wireless physical layer. The authors of[23]proposed a new two-level secure relay selection scheme in order to protect legitimate communication from eavesdropping. In [24], the authors considered a NOMA network with a halfduplex decode-and-forward relay to improve the physical layer security of two users. Two relay selection schemes termed decode-and-forward and amplify-and-forward protocols based optimal relay selection was proposed in[25].In[26],the authors proposed a novel cooperative NOMA scheme to guarantee the secure transmission of a specific user via two time slots.
Although scholars have provided many security schemes in the research of NOMA physical layer security,they rarely consider the dynamic confrontational interaction between the two parties.Using the method of game theory,this paper comprehensively considers the confrontation game relationship between the eavesdropper and the legitimate communicator, establishes the interaction behavior of the two sides as a zero-sum game model,and finally realizes the secure transmission of the legitimate communicator.
3 System Model
Consider the standard downlink transmission of a typical NOMA system, consisting of a base station(BS)equipped withNantennas,an external active eavesdropper(E),and two paired legitimate users(LU1andLU2)equipped with a single antenna respectively.In NOMA paired users,the user with better channel condition is called the strong user, and the user with poor channel gain is called the weak user[1].Without loss of generality,we assumeLU1is a strong user andLU2is a weak user.In our system model,BSsends signals to legitimate users,and the signals can also be received atEwho may decode the message from the received signals. Meanwhile,Emay sends jamming signal to the legitimate user to decrease its data rate and therefore the secrecy rate.In addition,we also assume thatEis only interested in the information ofLU2,the working mode ofLU1andLU2is half-duplex,and the working mode ofEis full-duplex,which can simultaneously eavesdrop and interfere and cause a certain amount of self-interference to oneself. In order to improve the security of the physical layer,two solutions are considered:superimposing artificial signal(AS)in the orthogonal null space in the transmission direction ofLU2and adding a relay station (RS) on the transmission link ofLU2, as shown in Figs.1a and 1b,respectively.
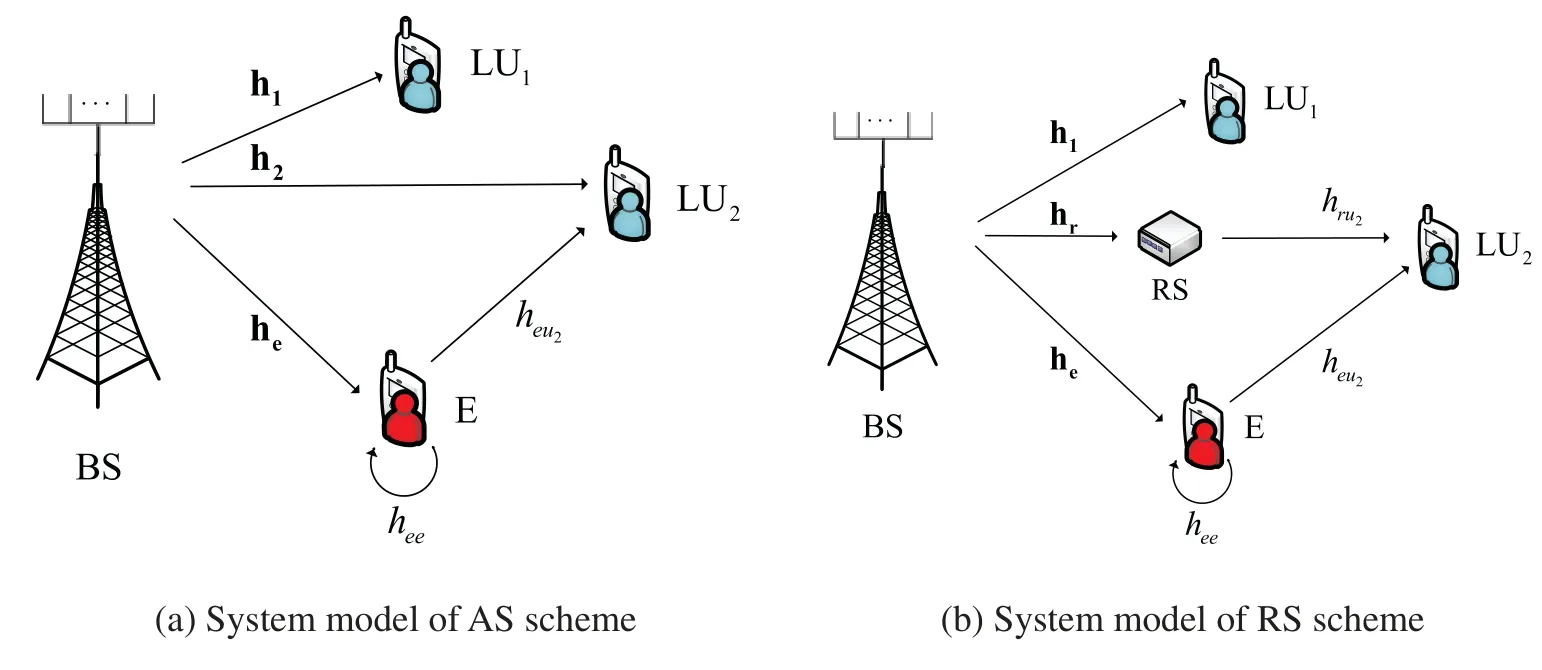
Figure 1:System model in AS and RS schemes
3.1 Channel Model
Assume that all channels experience independent quasi-static flat Rayleigh fading, where the channel coefficients remain unchanged within one time-frequency block but change independently between different time-frequency blocks, and suffer from additive white Gaussian noise (AWGN)[27,28].The 1×Nchannel gain vectors from theBStoLUi(i∈{1,2})andEare denoted as hi(i∈{1,2})and he,respectively.The channel vector fromEtoLU2is denoted asheu2,andE’s self-interference link gain ashee.Also,the 1×Nchannel gain vector from theBSto RS is denoted by hr,and the channel gain from RS toLU2is denoted byhru2.We denote the noise power atLU1,LU2,RS andEasandrespectively,with the same variance.We also assume that the quality of the relay channel in the system is better than that of the weak user,and the quality of the eavesdropping channel is worse than that of the weak user.It is reasonable to assume that the base stationBSknows the channel state information(CSI)of all channels betweenBSandLUi(i∈{1,2})perfectly due to the fact that they are normal transceivers in the NOMA system.
3.2 Signal Model
3.2.1 Signal Model of AS Scheme
In the system model of the AS scheme,the base station transmits superimposed signal to users.To protect the weak user from eavesdropping,the artificial signal is superimposed in the orthogonal null space of the transmission direction.The superimposed signal transmitted fromBStoLUi(i∈{1,2})can be expressed as

wherex1andx2are the information-carrying signals toLU1andLU2,x3is the artificial signal,Psis the power of effective signals in the superimposed signal at the base stationBS,P3is the transmission power of the artificial signal,α1andα2are the power sharing coefficients ofLU1andLU2at theBS, withα1+α2= 1 andα2>α1for user fairness,and w2are well designedN×1 beamforming vectors for effective signals and artificial signal,respectively,and(·)Hdenotes the Hermitian(conjugate)transpose operation.
Then,the signals received atLU1andLU2are given by

and
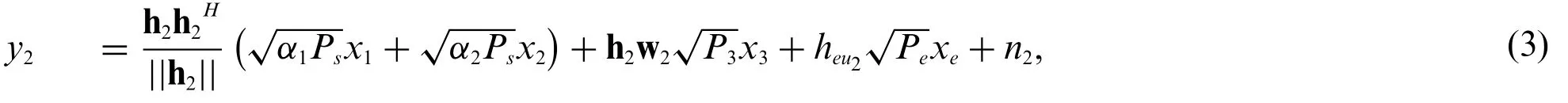
where hi~C N (0,λi),n1andn2are the additive white Gaussian noise(AWGN)atLU1andLU2,withni(i∈{1,2})~C N(0,σ2),whereC N (·,·)is the complex Gaussian distribution,xeandPerepresent the interference signal and its power emitted by the eavesdropperE.
Since the artificial signal is allocated into the orthogonal null space of the channel for NOMA users,we have h1w2=0 and h2w2=0[29].Then formulas(2)and(3)can be rewritten as

and

According to the power-domain NOMA principle, the strong user decodes his message by employing SIC after decoding the message of the weak user, and the weak user directly decodes his message by treating the signal of the strong user as noise.As a result,the signal-to-interference-to-noise ratio(SINR)atLU1in the process of decoding its own information is

and


Similarly,LU2decodes its own information directly,and the SINR can be expressed as


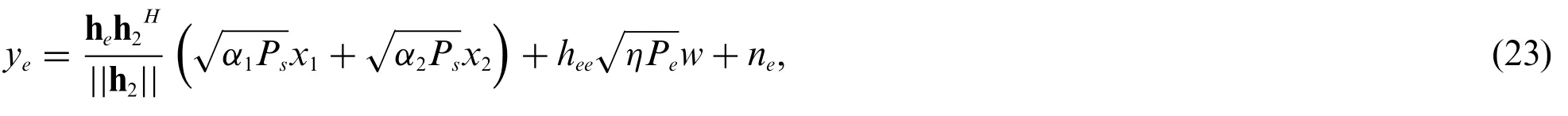
For the eavesdropperE,the received signal can be expressed as where he~C N (0,λe),ne~C N(0,σ2),andηis the residual self-interference coefficient.
The SINR at the eavesdropperEto decode the message forLU2can be expressed as


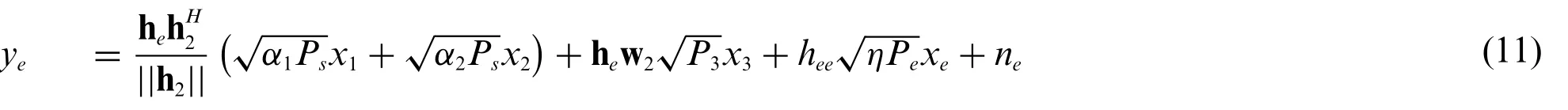
Similarly,when the eavesdropperEdoes not emit interference signals,i.e.,ρe=0,or theBSdoes not superimpose artificial signals,then we have
3.2.2 Signal Model of RS Scheme
In this scheme,the relay RS works in full duplex mode,and can decode and forward at the same time. In the transmission process, the base stationBSfirst transmits a superimposed signal to the legitimate userLU1and RS. After receiving the signal, the legitimate userLU1uses SIC technology to decode the signal to obtain its own message, and the relay RS decodes the message forLU2and forward it. Since the RS first decodes and then forward the message, it can perfectly eliminate the influence of self-interference [30]. The eavesdropperEeavesdrops at the base stationBS, emits an interference signal at a certain power level to the legitimate userLU2,and suffers from the influence of self-interference which cannot be perfectly eliminated.
In the system model of the RS scheme,the superimposed signal transmitted toLU1and RS at theBSis expressed as

The signals received atLU1and RS are respectively given by

and

where hr~C N (0,λr),nr~C N(0,σ2),and the rest variables are similar to that in the AS scheme.
The SINR at RS to decode the message forLU2can be expressed as

The legitimate userLU2receives the signal forwarded by the RS,which can be expressed as

wherehru2~C N0,λru2,heu2~C N0,λeu2,λru2andλeu2are the variance of complex Gaussian variableshru2andheu2,respectively,andPris the transmit power of RS to forward the message forLU2withPr=Ps.
The SINR atLU2to decode his own message can be expressed as

For such a link from theBStoLU2with the relay RS,the achievable data rate can be expressed as min■i.e.,with an equivalent SINR as

then the data rate forLU2can be expressed as

For the eavesdropperE,the received signal can be given as and the SINR at the eavesdropperEto decode the message forLU2can be expressed as

Similarly,when the eavesdropperEdoes not emit interference signals,i.e.,ρe=0,we have

4 Game Model
In this article,we assume that the eavesdropperEonly eavesdrops onLU2.Therefore,the secrecy rate of the system can be expressed as

where[·]+=max{·,0}.
In the downlink NOMA transmission system with external eavesdropperE, the legitimate userLU2exerts to maximize the secrecy rate, which means that he needs to increase his own data rate and/or reduce the eavesdropping rate ofE. On the contrary, for the eavesdropperE, he attempts to minimize the secrecy rate by increasing his own eavesdropping rate and/or reducing the data rate ofLU2.This shows that one person or group can gain something only by causing another person or group to lose it,and the sum of the gains and losses is always‘zero’.Therefore,we model the non-cooperative behavior between the legitimate users and the malicious eavesdropper in both AS and RS schemes as a non-cooperative two-person zero-sum game,respectively.
4.1 Game Modeling
4.1.1 Game Modeling for the AS Scheme
In the AS scheme,we regard the base stationBSand usersLUi(i∈{1,2})as a legitimate party,who can choose to transmit only the effective signals or the signals superimposed with artificial signal to improve the secrecy rate of the system.The eavesdropperEcan choose the strategy of only eavesdropping and not emitting the interference signal,or the strategy of eavesdropping while emitting the interference signal at the same time.We establish the zero-sum game model for secure downlink transmission in strategic form as follows.
Definition 4.1.In the AS scheme, the zero-sum gameG1= (N1,(Si)i∈N1,(ui)i∈N1)is a triplet,where:
•N1= {L,E}is a set of players in the game.Lrepresents the legitimate party consisting of the base stationBSand the legitimate usersLUi(i∈{1,2}),andErepresents the external malicious eavesdropper.
•Siis the set of possible strategies for playeri∈N1.ForL,its strategy set can be expressed asSL={A,O},whereArepresents the strategy of transmitting the effective signals superimposed with artificial signal, andOrepresents the strategy of transmitting only the effective signals without artificial signal. ForE, its strategy set can be expressed asSE= {I,N}, whereImeans eavesdropping and emitting interference signal at the same time, andNmeans only eavesdropping and not emitting interference signal.
•uiis the utility function of the playeri∈N1.In this paper,the secrecy rate of the system is taken as the utility function of the game.
According to Definition 4.1,we can further formulate the utility matrix for the zero-sum game,as shown in Table 1. In the utility matrix, there are four strategy profiles in all, and they are(A,I),(A,N),(O,I)and(O,N).Take the profile(A,I)for example,it means the legitimate partyLchooses the strategyAand the eavesdropper chooses the strategyI. We will analyze each strategy profile in detail and give their utility functions as follows.
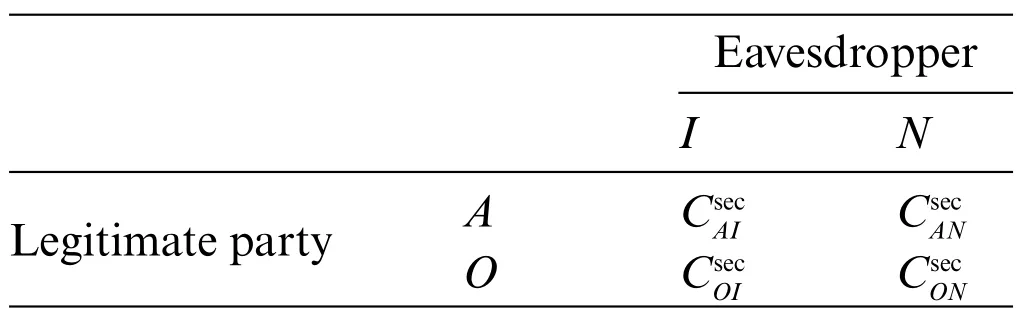
Table 1: Utility matrix of the zero-sum game in the AS scheme
For the profile(A,I),the legitimate partyLchooses to superimpose the artificial signal AS in the null space of the weak userLU2transmission direction to protect the message for the weak userLU2.The eavesdropperEchooses to emit an interference signal to the weak userLU2while eavesdropping.In such a profile,the utility function of the legitimate party can be expressed as
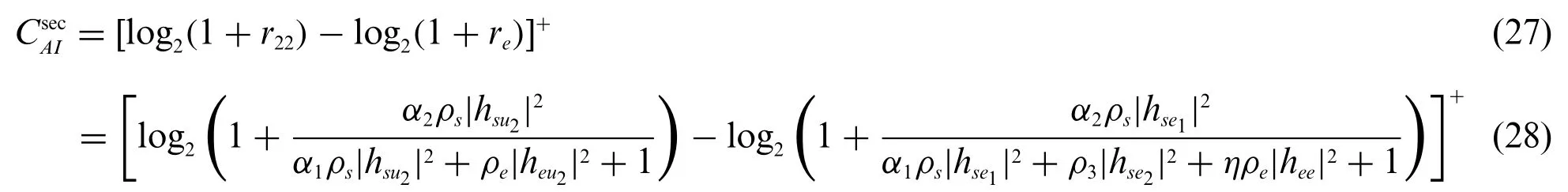
For the profile(A,N),the legitimate partyLchooses to superimpose the artificial signal AS in the null space of the transmission direction.At this time,the eavesdropperEchooses to eavesdrop only,i.e.,Pe=0.Then the utility function is given by
For the profile(O,I),the legitimate partyLchooses not to superimpose the artificial signal AS to protect the message forLU2,i.e.,P3=0.The eavesdropperEchooses to conduct both eavesdropping and interfering at the same time.The utility function can be expressed as
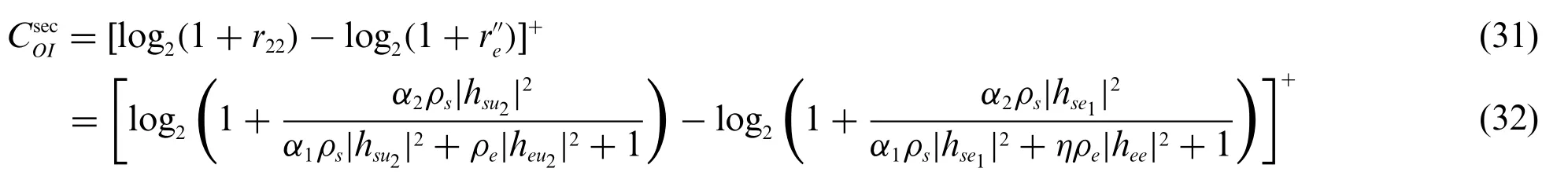
For the profile(O,N),the legitimate partyLdoes not choose the strategy of superimposing the artificial signal AS,and the eavesdropperEonly conducts wiretapping.Then,the utility function is given by

4.1.2 Game Modeling for the RS Scheme
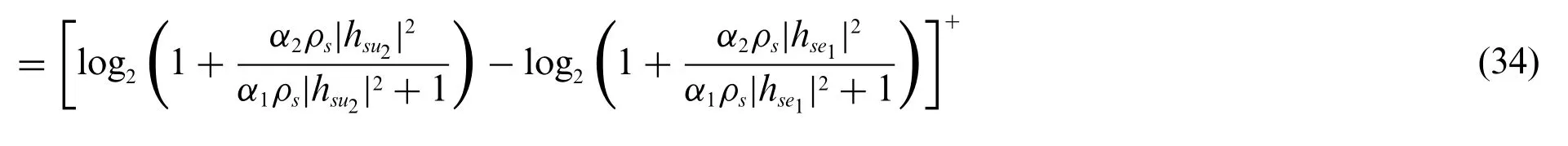
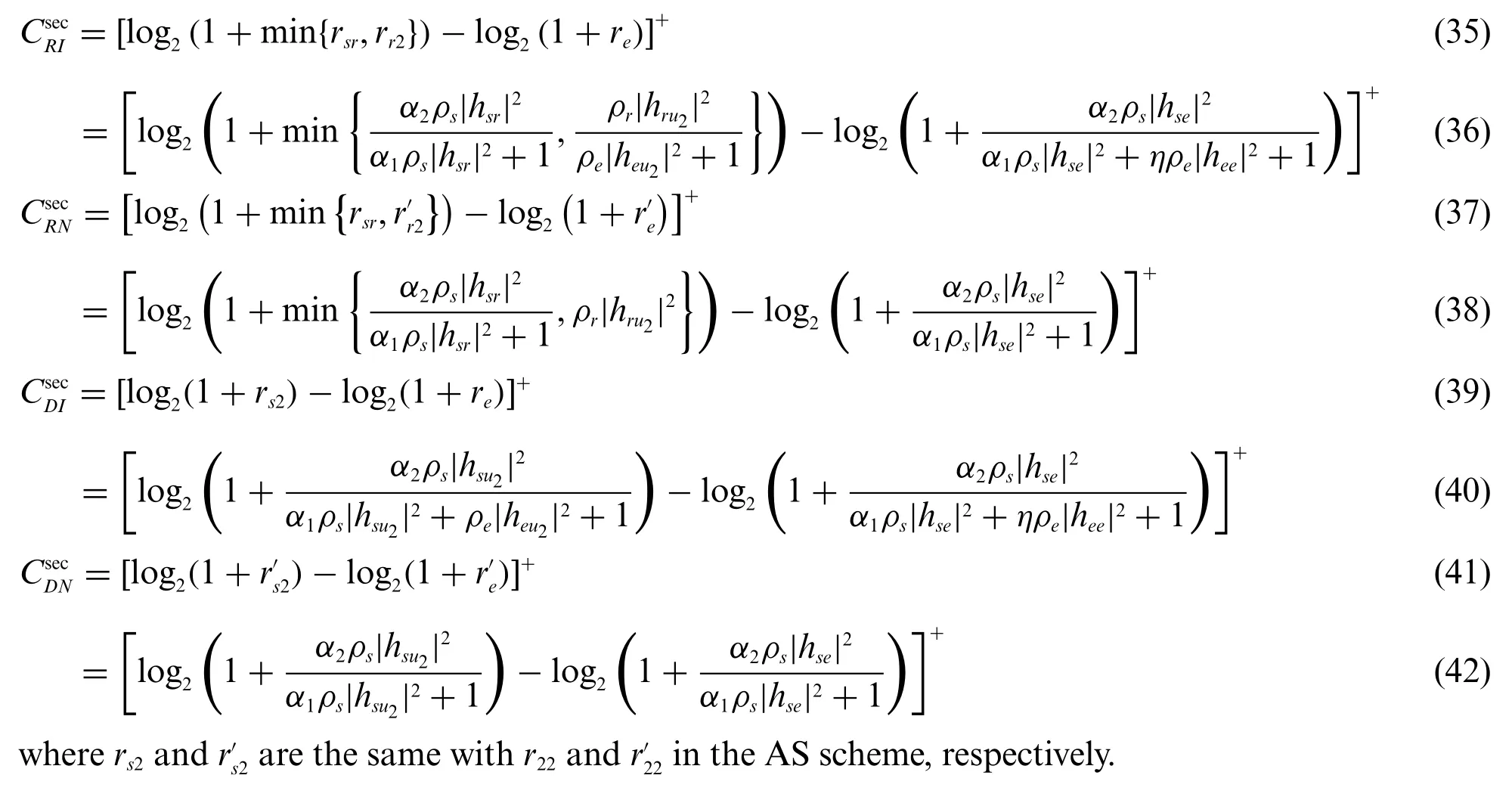
In the system model of the RS scheme, the legitimate partyLcan choose to use the relay transmission strategy or the direct link transmission strategy. The eavesdropperEcan choose from the strategies of eavesdropping strategy with or without emitting interference signal.We can establish the game model for the RS scheme as follows.
Definition 4.2.In the RS scheme, the zero-sum gameG2=is a triplet,where:
•N2= {L,E} is a set of players in the game. Same as in the gameG1,Ldenotes the legitimate communication party,andEthe eavesdropper.
•Sjis the set of available strategies for the playerj∈N2.ForL,its strategy set can be expressed asSL= {R,D},whereRrepresents the strategy of transmission with RS,andDrepresents the strategy of direct link transmission.ForE,its strategy set can be expressed asSE={I,N},whereImeans eavesdropping and emitting interference signals,andNmeans not emitting interference signals but only eavesdropping.
•ujis the utility function of the playerj∈N2.
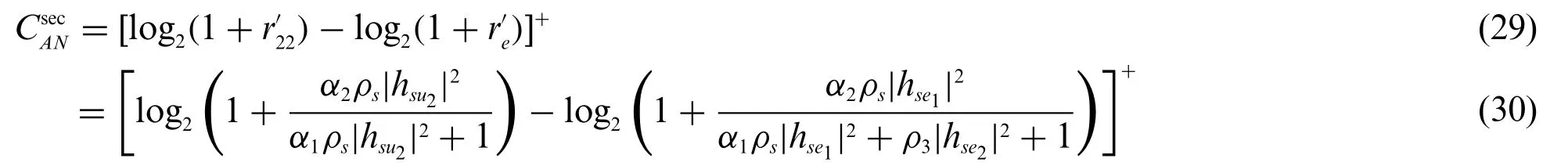
Similarly,we can formulate the utility matrix as shown in Table 2,and the utility functions can be expressed as follows:
4.2 Analysis of Game Equilibrium
In this subsection,we will first prove the existence of the Nash equilibrium for the zero-sum game in both AS and RS schemes,and then solve and analyze the pure strategy Nash equilibrium and the mixed strategy Nash equilibrium,respectively.
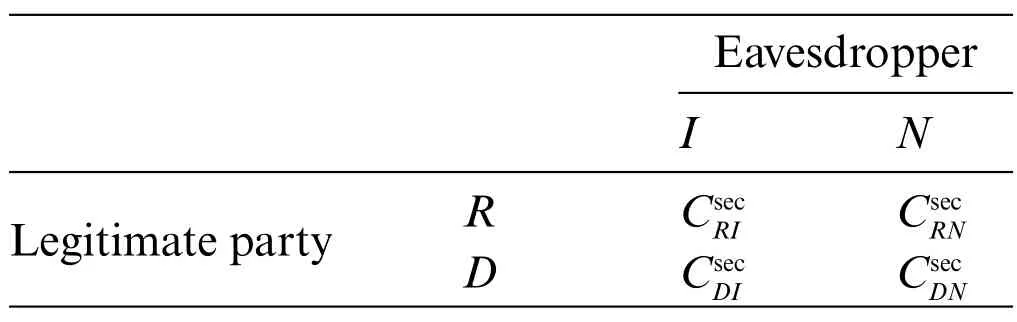
Table 2: Utility matrix of the zero-sum game in the RS scheme
4.2.1 Existence of NE
We give the results of Nash Equilibrium of the gamesG1andG2by the following two theorems.
Theorem 4.1.There is at least one Nash equilibrium in the zero-sum gameG1of the AS scheme.
Proof.In the zero-sum gameG1,the set of playersN1= {L,E}has two players,which is limited.Additionally, the set of strategiesSL= {A,O} andSE= {I,N} are both limited. According to the existence theorem of Nash equilibrium,there is at least one Nash equilibrium in the gameG1.
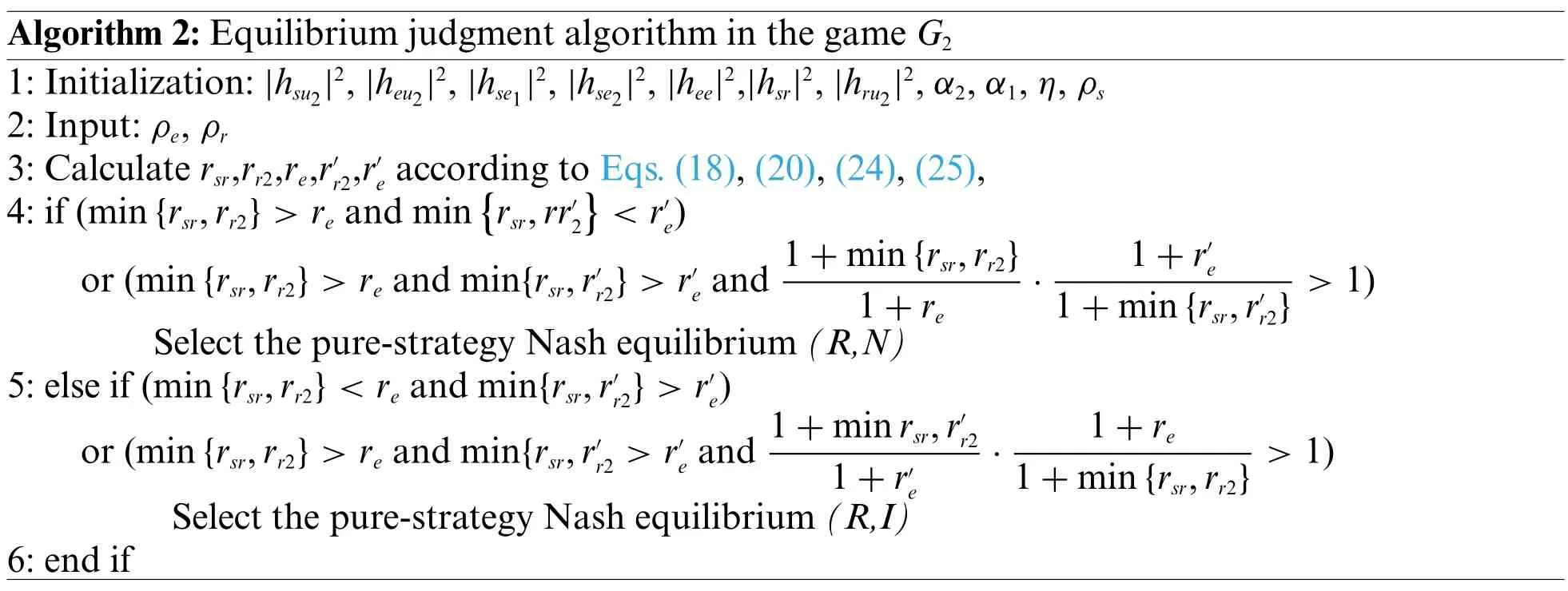
Theorem 4.2.There is at least one Nash equilibrium in the zero-sum gameG2of the RS scheme.
The proof is similar to that of Theorem 4.1 and thus omitted for simplicity.
4.2.2 Pure-strategy Nash Equilibrium
In this subsection,we solve the pure-strategy Nash equilibrium of the gameG1andG2,respectively.The pure-strategy Nash equilibrium and the corresponding strategies for the games in AS and RS schemes are provided by the following two theorems.
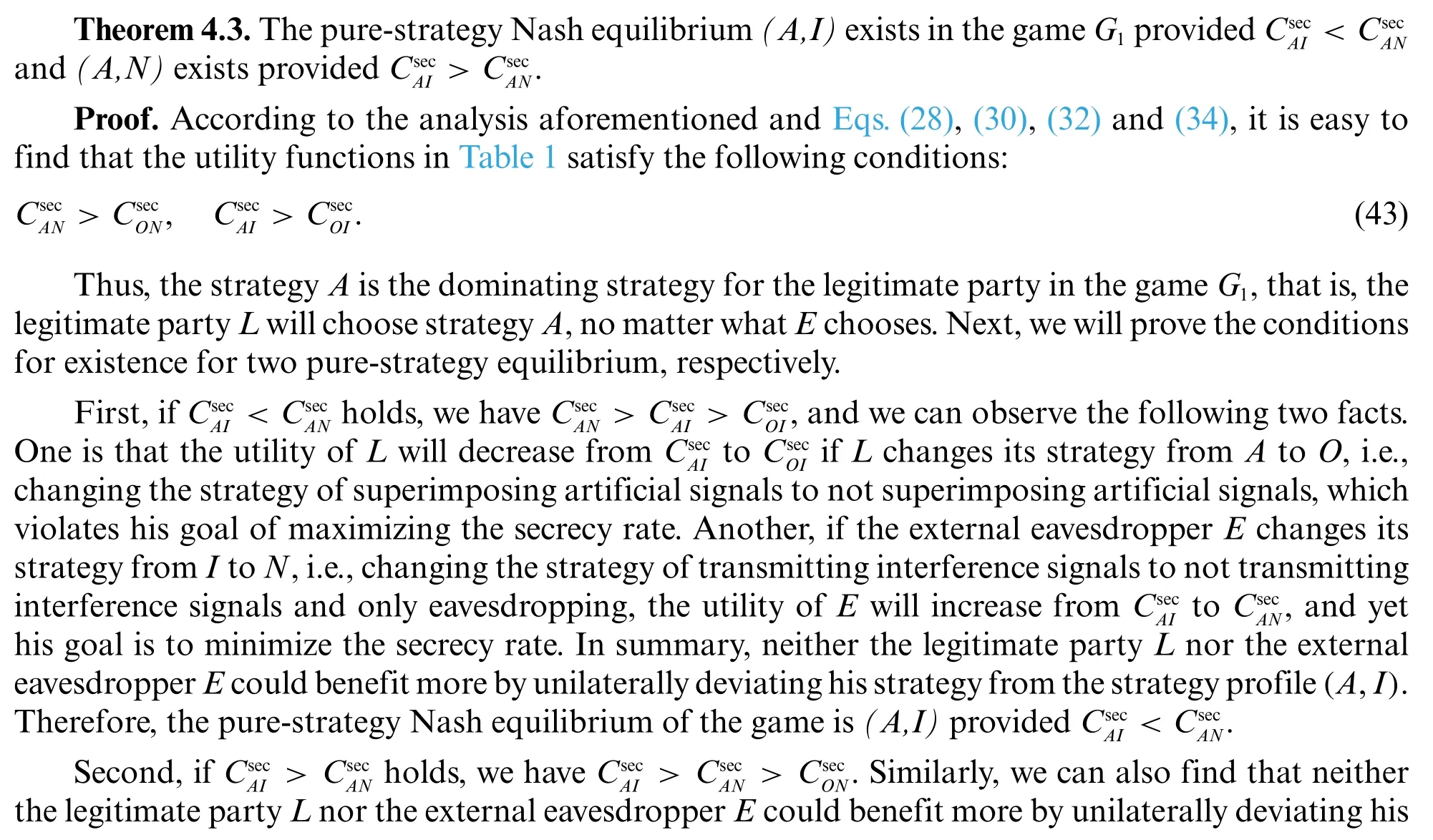
Thus,the strategyRis the dominating strategy for the legitimate party in the gameG2,that is,the legitimate partyLwill choose strategyR,no matter whatEchooses.Next,we will prove the conditions for existence for two pure-strategy equilibrium,respectively.

This completes the proof.
4.2.3 Algorithms for Pure Strategy Nash Equilibrium Strategy
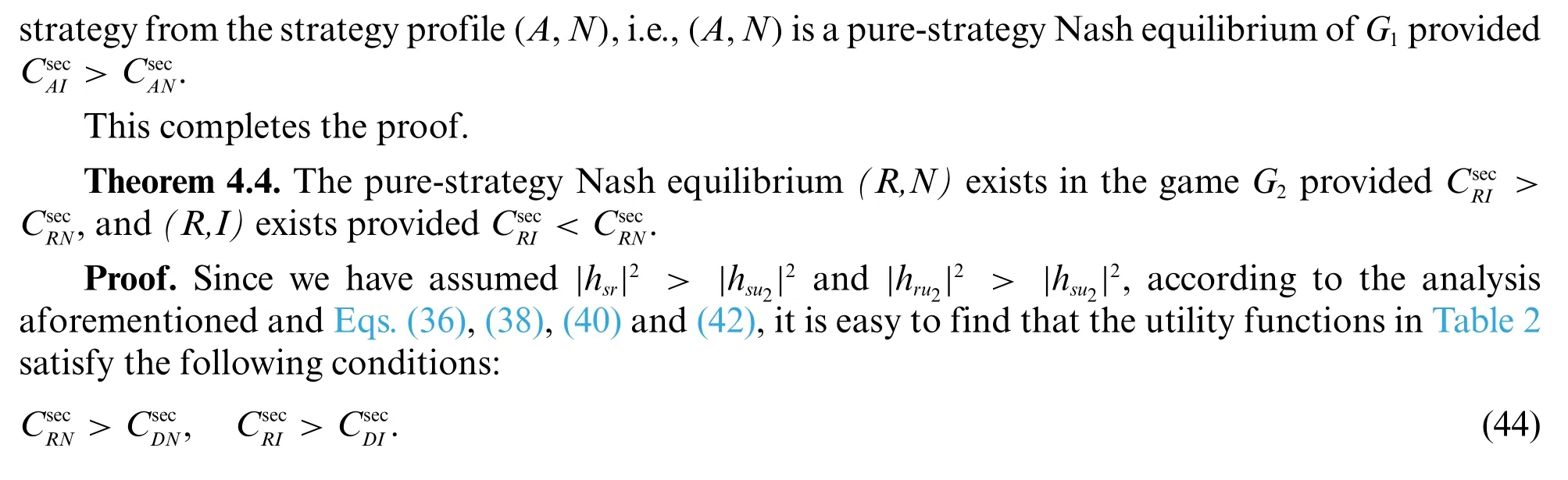
According to the analysis in the previous section, there are two situations in the pure strategy Nash equilibrium of the gameG1andG2.Therefore,we propose two algorithms to determine the pure strategy Nash equilibrium strategy.The algorithms are described as follows.

Algorithm 1:Equilibrium judgment algorithm in the game G1 1:Initialization:|hsu2|2,|heu2|2,|hse1|2,|hse2|2,|hee|2,α2,α1,η,ρs 2:Input:ρe,ρ3 3:Calculate r22,re,r'22,r'e according to Eqs.(9),(12),(14),(15),4:if(r'22 >r'e and r22 <re)or(r22 >re and 1+r22'1+r22·1+re 1+r'e>1)Select the pure-strategy Nash equilibrium(A,I)5:else if(r'22 <r'e and r22 >re)or(r'22 >r'e and 1+r22 1+r'22·1+r'e 1+re>1)Select the pure-strategy Nash equilibrium(A,N)6:end if
Algorithm 2:Equilibrium judgment algorithm in the game G2 1:Initialization:|hsu2|2,|heu2|2,|hse1|2,|hse2|2,|hee|2,|hsr|2,|hru2|2,α2,α1,η,ρs 2:Input:ρe,ρr 3:Calculate rsr,rr2,re,r'r2,r'e according to Eqs.(18),(20),(24),(25),4:if(min{rsr,rr2}>re and min■rsr,rr'2■<r'e)or(min{rsr,rr2}>re and min{rsr,r'r2}>r'e and 1+min{rsr,rr2}1+re· 1+r'e 1+min{rsr,r'r2} >1)Select the pure-strategy Nash equilibrium(R,N)5:else if(min{rsr,rr2}<re and min{rsr,r'r2}>r'e)or(min{rsr,rr2}>re and min{rsr,r'r2 >r'e and 1+min rsr,r'r2 1+r'e· 1+re 1+min{rsr,rr2} >1)Select the pure-strategy Nash equilibrium(R,I)6:end if
4.2.4 Mixed-Strategy Nash Equilibrium
Different from the deterministic selection of a strategy in pure-strategy Nash equilibrium,a player may select each pure strategy with a certain probability,which leads to the concept of a mixed strategy.For each player,a mixed strategy consists of a number of possible actions and a probability distribution which corresponds to how frequently each action would be selected by the player.In this subsection,we will discuss the mixed-strategy Nash equilibrium of the gameG1andG2,respectively.
The mixed strategy Nash equilibrium in AS and RS schemes are given by the following two theorems.
Theorem 4.5.The utility of the mixed strategy Nash equilibrium(p*,q*)of the gameG1is written as

Proof.In the AS scheme,we define the probability distributionP=(p,1-p)for the legitimate partyL,where 0 ≤p≤1 is the probability with whichLselects the strategyA,i.e.,the selection of superimposing artificial signals. Hence, 1-pis the probability with whichLselects the strategyO.Similarly,we define the mixed strategy for the eavesdropperEasQ=(q,1-q),where 0 ≤q≤1 is the probability with whichEselects the strategyI,i.e.,the selection of emitting interference signals,and 1-qthe probability of selecting the strategyN.Hence,the utility of the mixed strategy can be expressed asU(p,q)=PCQT.
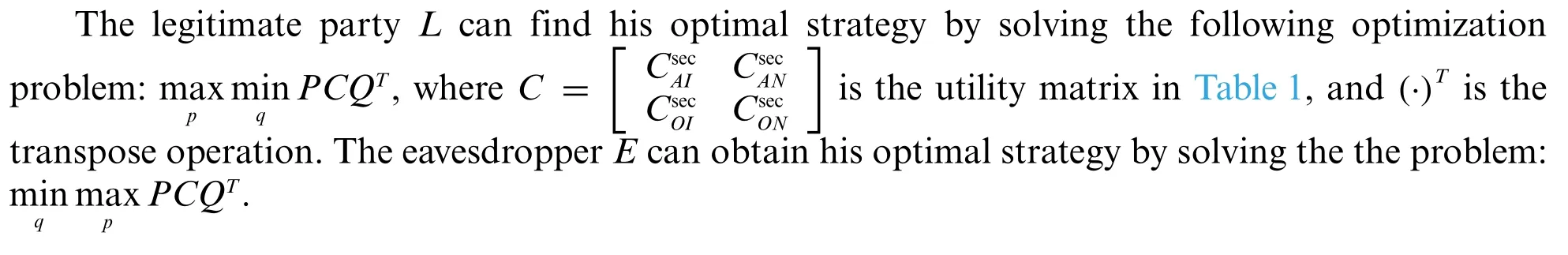
Solving the above two optimization problem yields the optimal probability value of each strategy selected byLandEas
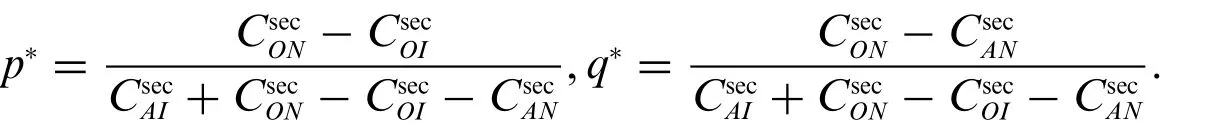
Then substitutep*andq*intoPCQT, the Nash equilibrium utility of the mixed strategy of the gameG1is written as
This completes the proof.
Theorem 4.6.The utility of the mixed strategy Nash equilibrium(p*,q*)of the gameG2is written as
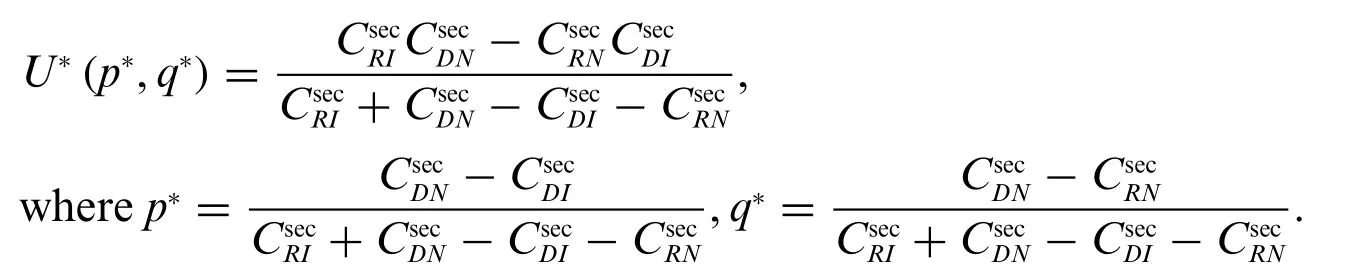
The proof is similar to Theorem 4.5,and thus omitted for simplicity.
5 Numerical Simulation and Result Analysis
5.1 Simulation Setting
The main parameter settings in the simulation of AS and RS scheme are as follows. The power allocation coefficients of strong users and weak users in the NOMA system areα1= 0.2,α2= 0.8,respectively,the transmission signal-to-noise ratio at each node ranges from 0 to 30 dB,and the residual self-interference coefficientηduring the process of eavesdropping transmitting interference power is 0.1.
5.2 Result Analysis in the AS Scheme
This subsection mainly analyzes the data rate of the weak user and the eavesdropper, as well as the gains of the pure and mixed strategy in the AS scheme.
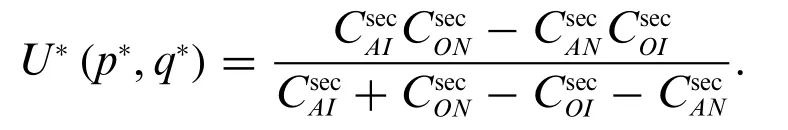
5.2.1 Analysis of Data Rate
The curves in Fig.2a show the data rateR2ofLU2with respect toρsunder differentρein the AS scheme.It can be seen from the figure that whenρeis constant,R2increases asρsincreases;whenρsis constant,R2decreases asρeincreases,which implies that,when the power of the interference signal transmitted byEis larger,the information transmission rate ofLU2can be reduced,so that the security rate of the system is smaller,and its purpose can be achieved.The legitimate partyLcan appropriately increase the total transmission power to weaken the influence ofEinterference.
Fig.2b shows the change of the data rate ofEwithρ3in the AS scheme. It can be seen from the figure that whenρeis constant,Redecreases asρ3increases; whenρ3is constant,Redecreases asρeincreases. It shows that whileEis transmitting interference signals, although it can reduce the information transmission rate ofLU2, it will also reduce its own information transmission rate.Therefore,Eneeds to consider the power value of the transmitted interference signal in the game.The legitimate party can reduceReby increasing the power of the artificial signal,thereby increasing the security rate of the system and improving the security of the physical layer.
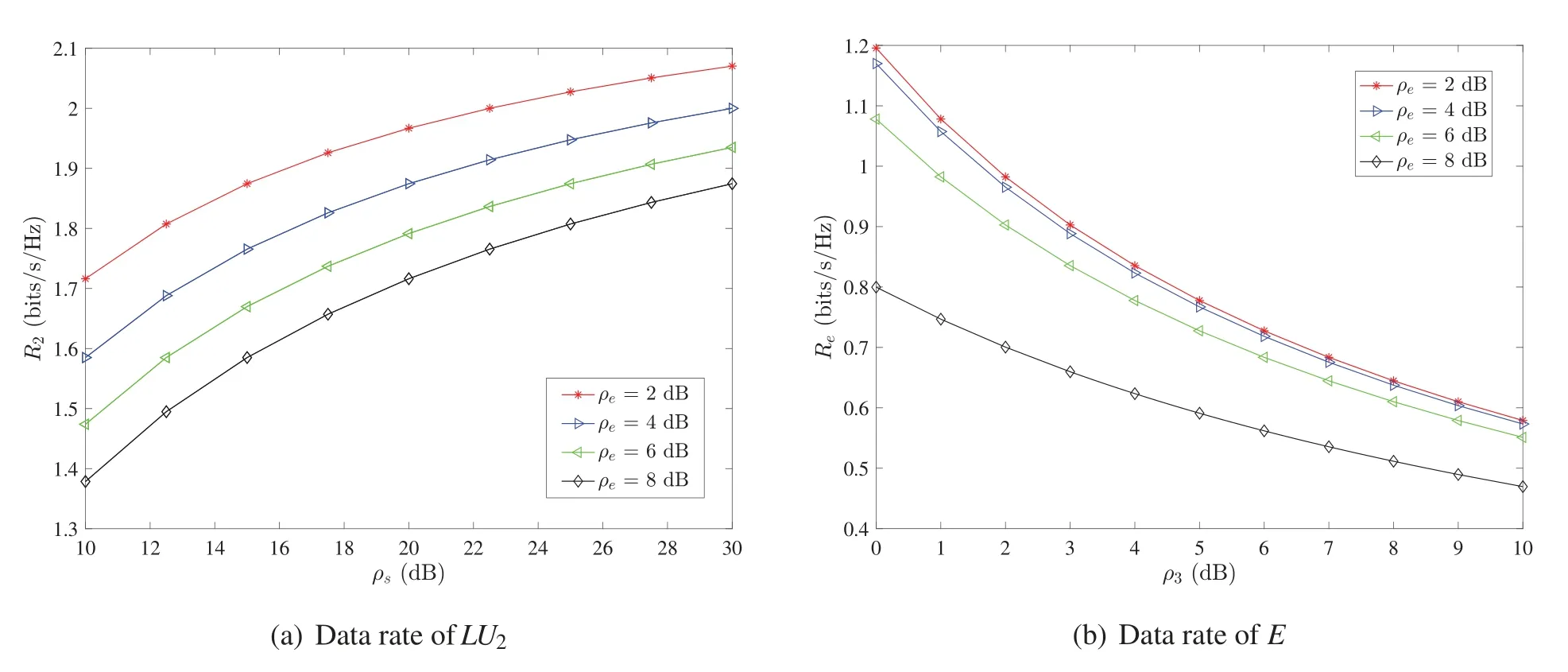
Figure 2:Data rate in the AS scheme
5.2.2 Analysis of the Pure Strategy Nash Equilibrium and Benefits
According to the aforementioned analysis, the pure strategy Nash equilibrium depends on the parameterρeandρ3.We show the effect ofρeandρ3on the pure strategy Nash equilibrium in Fig.3,and we can find the following results.First,the equilibrium strategy changes from(A,N)to(A,I)asρeincreases ifρ3<M.Second,ifρ3>Mthe equilibrium strategy stays at(A,I)no matter howρechanges.We also have similar results forρe,ρ3and some pointM'at the axis ofρe.

Figure 3:Effect of ρe and ρ3 with ρs =30 dB on pure strategy Nash equilibrium in the AS scheme


Figure 4:The benefits of pure strategy in the AS scheme
Likewise,from Fig.4b,we can get similar results that the equilibrium strategy and the corresponding benefit is(A,N)andwhen 0<ρe <X(B),and the equilibrium strategy and the corresponding benefit is(A,I)andwhenρe >X(B).
5.2.3 Analysis of the Mixed Strategy Benefits
Fig.5 shows the benefit variation of the mixed strategy in the AS scheme with respect toρs. It can be seen from the figure that the revenue of the mixed strategy under AS scheme increases with the increase ofρs.The red curve represents the mixed strategy benefits under the best probability value,and the other three curves represent the mixed strategy benefits when±ε,±2εand±3εare offset on the basis of the best probability value.The figure shows that the benefits of the mixed strategy under the optimal probability is the best,which verifies the previous theoretical analysis results.
Fig.6 shows the comparison of benefits between the pure strategy Nash equilibrium and the mixed strategy Nash equilibrium in the AS scheme.From the local enlarged subplot,we can clearly find that the benefit curves of potential pure strategy Nash equilibrium profiles(A,I),(A,N)and the mixed strategy Nash equilibrium intersect at pointX,YandZ. With the increase ofρs, the equilibrium strategy profile will change from(A,I)to(A,N)whenρsgoes across the abscissa ofZif the mixed strategy is not considered.Instead,if the mixed strategy is taken into consideration,the equilibrium strategy profile will change from(A,I)to the mixed strategy whenρsgoes across the abscissa ofX.
Additionally,from Fig.6,we can see that the curve of random-selection method is always below the curves of pure and mixed strategy NE.This is not good for legitimate communicators.Therefore,the legitimate communication party will not select the random-selection strategy to increase the secrecy rate,i.e.,the random-selection strategy is unstable in the AS scheme.
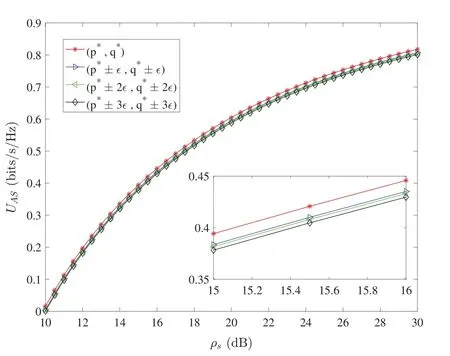
Figure 5:Benefits of mixed strategies in the AS scheme
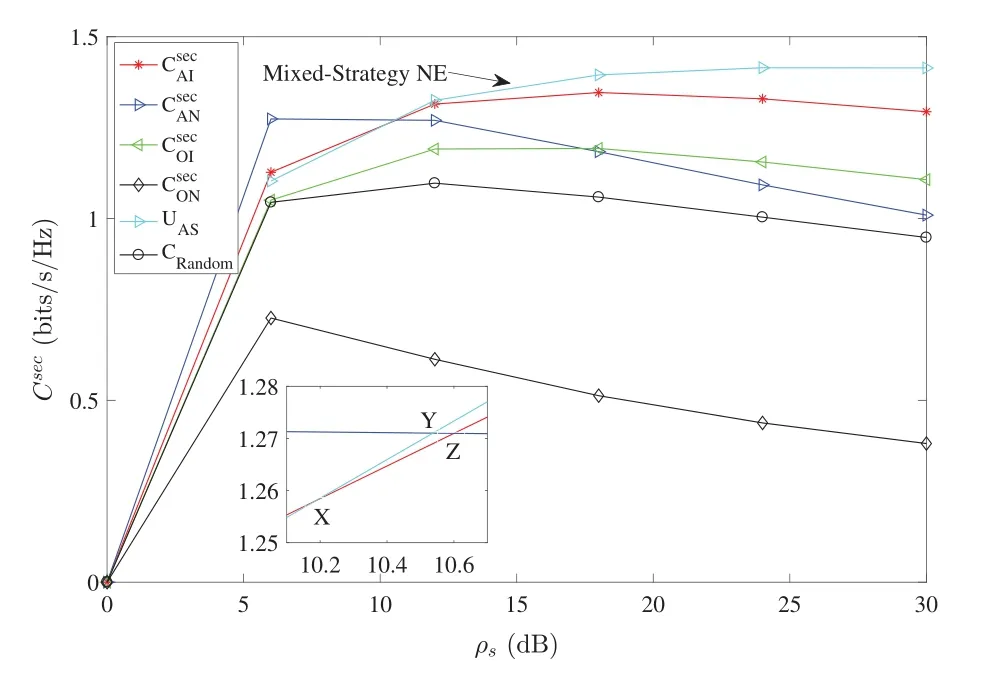
Figure 6:Comparison of the benefits between pure and mixed strategy NE in the AS scheme
5.3 Result Analysis in the RS Scheme
This subsection mainly analyzes the data rate of the weak user and the eavesdropper, as well as the benefits of the pure and mixed strategy in the RS schemes.
5.3.1 Analysis of Data Rate
Fig.7a shows the relationship between the information transmission rate ofLU2and the selection of different strategies in the RS scheme.We can see that when the legitimate party selects strategy‘R’(add relay),the information transmission rate ofLU2is better than that of strategy‘D’(direct link).It shows that the RS scheme can improve the physical layer security performance of the system.
Fig.7b shows the relationship between the information transmission rate ofEandρsin the RS scheme.Whenρeis constant,Reincreases with the increase ofρs;whenρsis constant,Redecreases with the increase ofρe.This shows that ifEincreases the power of transmitting interference signals,its own transmission rate will be reduced,and the security rate of the system will increase.If the legitimate party blindly increases the total transmission power,the security rate of the system will decrease.Therefore,in order to achieve their respective goals,both parties need to choose an appropriate power value.
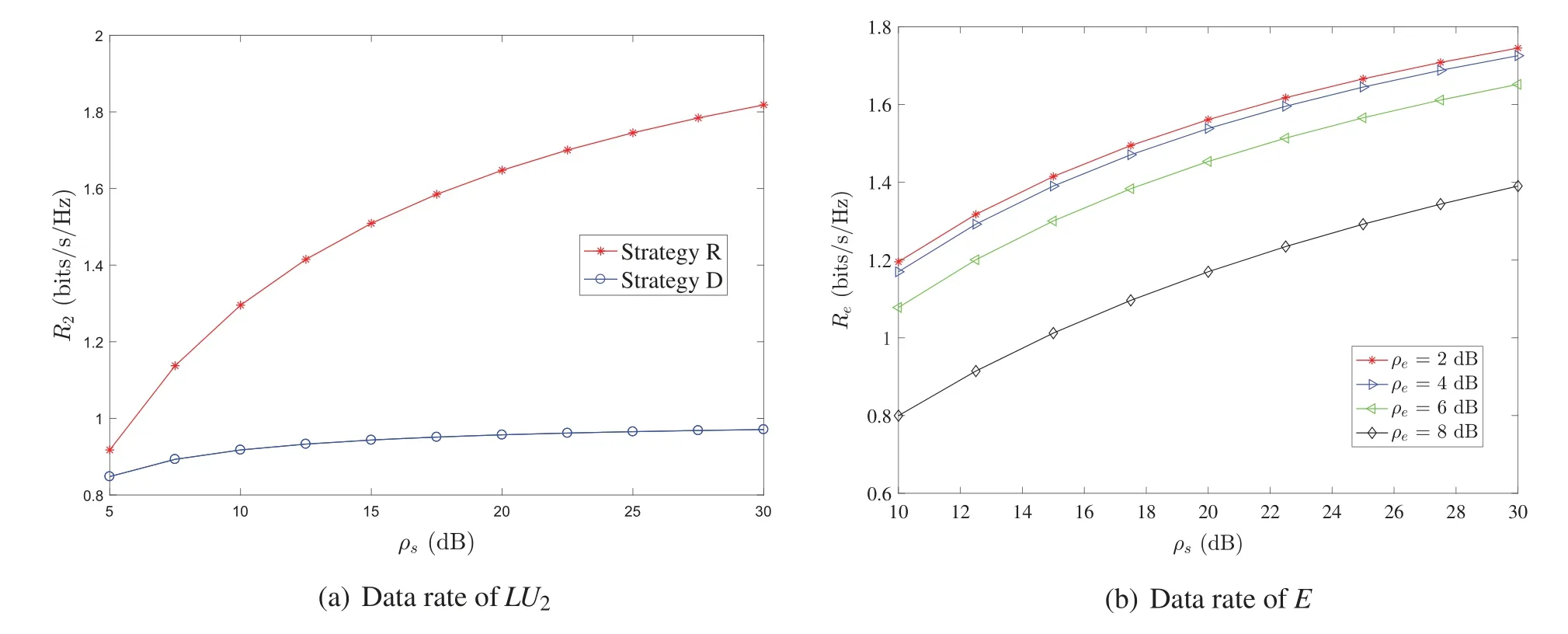
Figure 7:Data rate in the RS scheme
5.3.2 Analysis of the Pure Strategy Nash Equilibrium and Benefits
According to the analysis,the pure strategy Nash equilibrium depends on the parameterρeandρs.We show the effect ofρeandρson the pure strategy Nash equilibrium in Fig.8,and we can find the following results.First,ifρskeeps constant,the equilibrium strategy changes from(R,N)to(R,I)asρeincreases.Second,ifρekeeps constant,the equilibrium strategy changes from(R,I)to(R,N)asρsincreases.
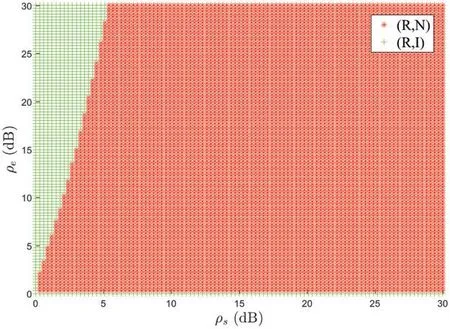
Figure 8:Effect of ρe and ρs on pure strategy Nash equilibrium in the RS scheme
Fig.9 shows the pure strategy benefits under different conditions in the zero sum game of RS scheme.Fig.9a shows the change of pure strategy benefits withρs,and Fig.9b shows the change of pure strategy benefits withρe.It can be seen from the figure that the benefits of the pure strategy Nash equilibrium isWhen the legitimate party changes strategy‘R’to‘D’,the benefits will change fromtoWhen the eavesdropper changes strategy‘N’to‘I’,the revenue will increase fromto
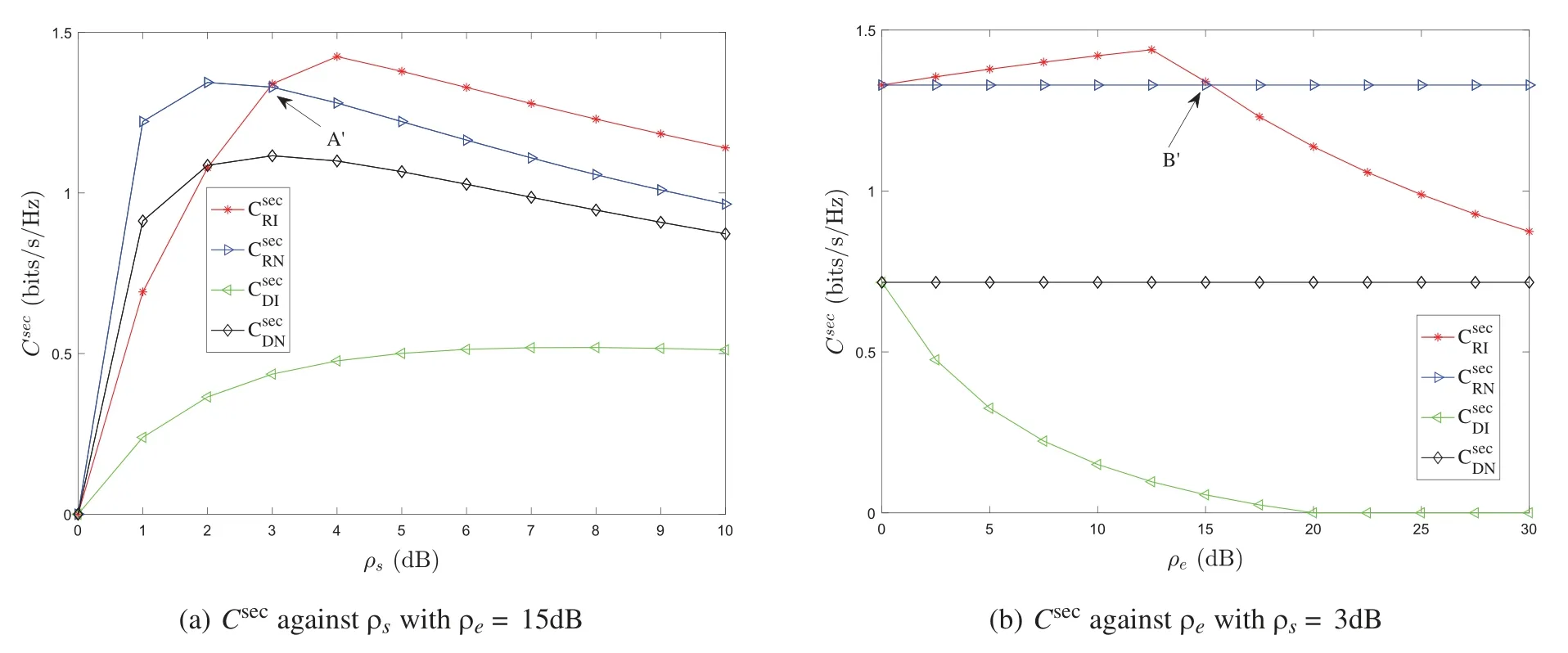
Figure 9:The benefits of pure strategy in the RS scheme
5.3.3 Analysis of the Mixed Strategy Benefits
Fig.10 shows the change of the mixed strategy benefits of the zero sum game of RS scheme withρs.It can be seen from the figure that the mixed strategy benefits under RS scheme decreases with the increases ofρs.The red curve represents the mixed strategy benefits under the best probability value,and the other three curves represent the mixed strategy benefits when ±ε, ±2εand ±3εare offset on the basis of the best probability value. The mixed strategy benefits the most under the optimal probability value,that is,the Nash equilibrium value of the mixed strategy.
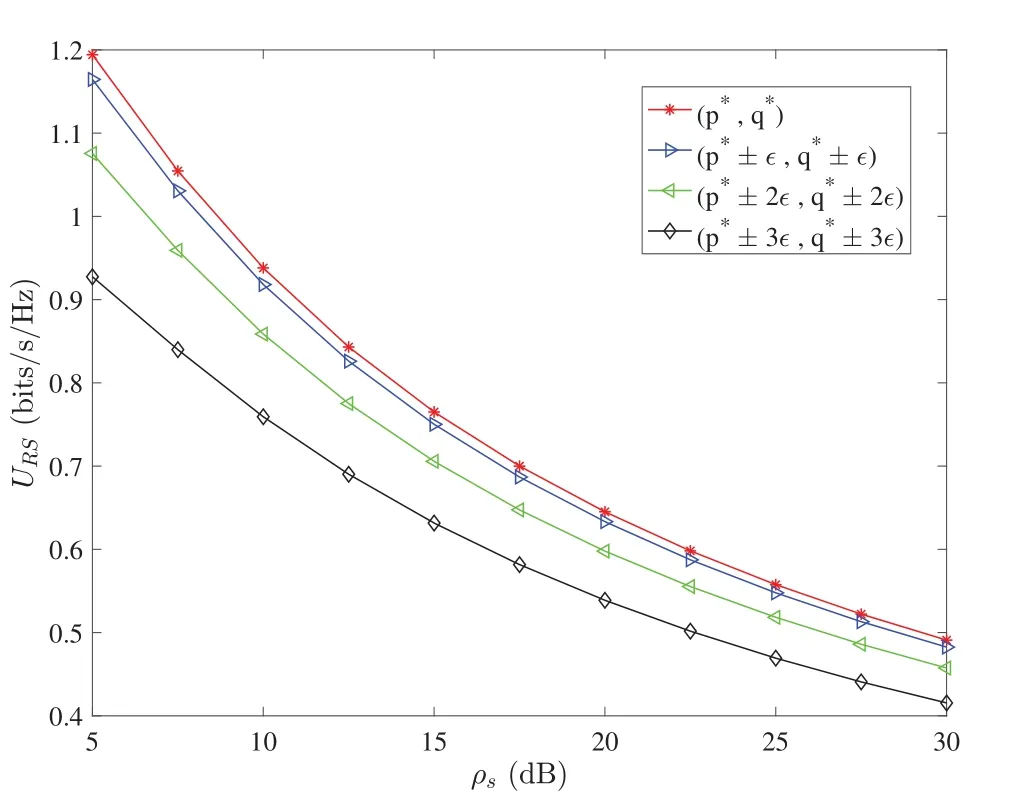
Figure 10:Benefits of mixed strategies in the RS scheme
Fig.11 shows the comparison of benefits between the pure strategy Nash equilibrium and the mixed strategy Nash equilibrium in the RS scheme.It can be seen that the benefits of the mixed strategy Nash equilibrium are always smaller than that of the pure strategy Nash equilibrium.Therefore,both sides of the game will always choose a pure strategy.That is to say,in the zero-sum game of the RS scheme, both sides will choose the pure strategy NE profile(R,N), that is, the legitimate partyLchooses the strategy of adding a relay station, and the eavesdropperEchooses the eavesdropping strategy.
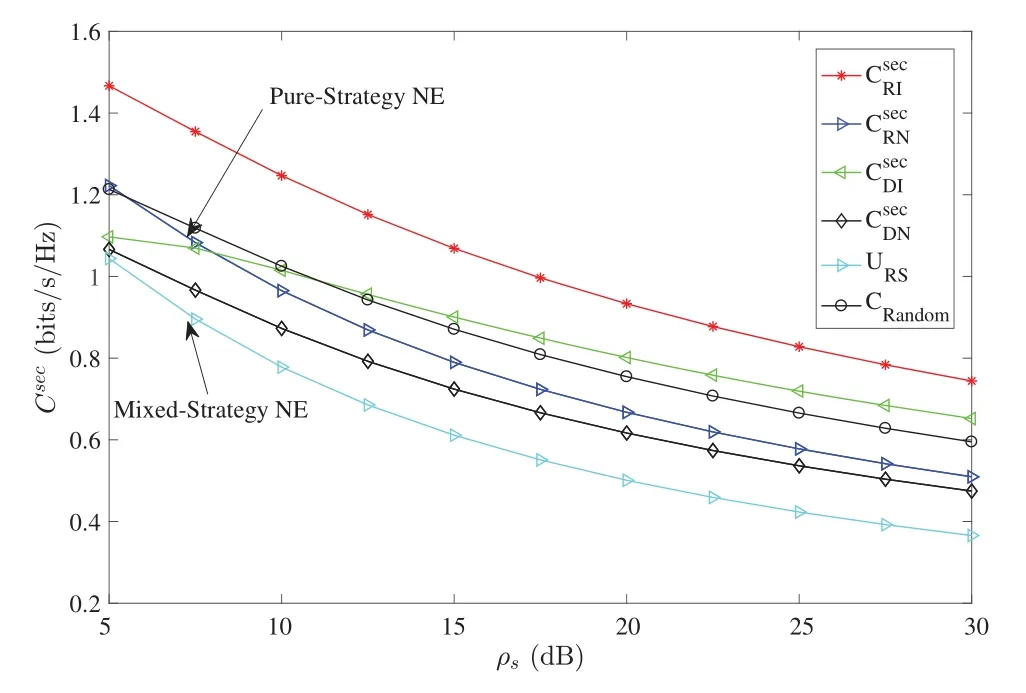
Figure 11:Comparison of the benefits between pure and mixed strategy NE in the RS scheme
Additionally,from Fig.11,we can observe that the curve of random-selection method is always above the curves of pure and mixed strategy NE. This is not good for the active eavesdropper.Therefore,the active eavesdropper will not select the random-selection strategy to decrease the secrecy rate,i.e.,the random-selection strategy is also unstable in the RS scheme.
6 Conclusion
In the scenario of the standard downlink NOMA transmission system,this paper considers two typical physical layer security design schemes based on artificial signals and relay assistance.The noncooperative behavior between the legitimate communication party and the eavesdropping party under the two schemes is modeled as a two-person zero-sum game. The game is used to characterize the confrontational behavior relationship between the two parties and the process of mutual influence,and prove the existence of the game Nash equilibrium.Through the solution and analysis of the pure strategy and mixed strategy Nash equilibrium of the security game model, the best strategy profile of the two parties in the confrontation environment is given.Numerical simulation results show that both solutions can improve the physical layer security of the NOMA system.The physical layer security game model proposed in this paper can be extended to other scenarios(such as the combination of relay and artificial signals)and can be used to guide the analysis and design of security solutions.However,the cases where there are multiple eavesdroppers and multi-user pairs have not been considered in this paper,and need to be studied in the future.
Acknowledgement:The authors wish to express their appreciation to the reviewers for their helpful suggestions which greatly improved the presentation of this paper.
Funding Statement:This research was supported by the National Natural Science Foundation of China under Grants U1836104, 61801073, 61931004, 62072250, National Key Research and Development Program of China under Grant 2021QY0700,and The Startup Foundation for Introducing Talent of NUIST under Grant 2021r039.
Conflicts of Interest:The authors declare that they have no conflicts of interest to report regarding the present study.
杂志排行
Computer Modeling In Engineering&Sciences的其它文章
- Edge Intelligence with Distributed Processing of DNNs:A Survey
- Turbulent Kinetic Energy of Flow during Inhale and Exhale to Characterize the Severity of Obstructive Sleep Apnea Patient
- The Effects of the Particle Size Ratio on the Behaviors of Binary Granular Materials
- A Novel Light Weight CNN Framework Integrated with Marine Predator Optimization for the Assessment of Tear Film-Lipid Layer Patterns
- Implementation of Rapid Code Transformation Process Using Deep Learning Approaches
- A New Hybrid Hierarchical Parallel Algorithm to Enhance the Performance of Large-Scale Structural Analysis Based on Heterogeneous Multicore Clusters
