Unidirectional Identity-Based Proxy Re-Signature with Key Insulation in EHR Sharing System
2022-07-02YananChenTingYaoHaipingRenandZehaoGan
Yanan Chen,Ting Yao,Haiping Ren and Zehao Gan
1School of Information and Software Engineering,University of Electronic Science and Technology of China,Chengdu,610054,China
2Basic Course Teaching Department,Jiangxi University of Science and Technology,Nanchang,330013,China
3Institute of Electronic and Information Engineering,University of Electronic Science and Technology of China,Dongguan,523808,China
4Network and Data Security Key Laboratory of Sichuan Province,Unversity of Electronic Science and Technology of China,Chengdu,610054,China
ABSTRACT The introduction of the electronic medical record (EHR) sharing system has made a great contribution to the management and sharing of healthcare data.Considering referral treatment for patients,the original signature needs to be converted into a re-signature that can be verified by the new organization.Proxy re-signature(PRS)can be applied to this scenario so that authenticity and nonrepudiation can still be insured for data.Unfortunately,the existing PRS schemes cannot realize forward and backward security.Therefore,this paper proposes the first PRS scheme that can provide key-insulated property,which can guarantee both the forward and backward security of the key.Although the leakage of the private key occurs at a certain moment,the forward and backward key will not
KEYWORDS Proxy re-signature;key insulation;electronic medical record (EHR);random oracle model
1 Introduction
With the improvement of living standards,the healthcare field has attracted more awareness and is playing an increasingly crucial role [1,2].At the same time,with the aging of the population,the demand for online healthcare treatment is rising.Therefore,the data that the hospital needs to manage is enormous,resulting in a mass of health data that needs to be stored and maintained.The introduction of electronic medical records (EHRs) can solve this problem well,that is,storing and using patient medical records including personal information through the integration of the Internet of Things (IoT),deep learning,blockchain,and other technologies[3–6].Compared with the conventional method of using paper to preserve health records,it is more advantageous and convenient to analyze the condition and manage the data in EHR sharing system.Nevertheless,putting health records on the Internet in electronic form will inevitably cause security problems.For the confidentiality of information in the IoT environment,there are already various effective methods to encrypt and protect them [7–11],but it is not enough to have only encryption means,and the authenticity of the message needs to be determined.Any unauthorized changes in data will affect the diagnosis and timely treatment of the disease,thus the integrity of the data must be guaranteed.Generally,digital signatures are used to ensure whether the data has been tampered with or not [12–15].However,when a patient needs to be referred for treatment,for example,a physician in the hospital needs to give the patient’s EHR to the researcher in the institution for further study.In this case,the signature generated by the hospital demands to be converted into the signature under the institution.Traditionally,the institution is required to verify the legality of the signature first and then recompute its own signature.To make matters worse,there are plenty of data to be processed in the EHR sharing system,which is difficult for the institution with limited resources or inconvenient situations.Therefore,the task of converting signatures can be entrusted to the semi-trusted proxy—an insurance company.The technology of proxy re-signature (PRS) can implement the transform requirement,while the proxy can not completely replace the hospital or institution and create any other signatures belonging to them without receiving the authorization and delegation.Through the interaction with the delegator,the signature belonging to the delegatee can be converted into the delegator by proxy.What’s more,the conversion process can be completed without the private key of the delegatee,that is,the delegatee does not need actual interactive participation.Accordingly,the concept of PRS can be applied to transfer electronic medical records for management scenarios in EHRs.
However,in a complex environment,the problem of key exposure arises.Once the user is compromised,the attacker can completely pretend to be the user and do whatever he wants,which is definitely fatal.In 2009,Yang et al.[16] combined the two primitives of PRS and forwardsecure threshold signature to construct the first forward-secure threshold proxy re-signature scheme.The re-signature key will be updated in different time periods,thus if the re-signature key is leaked in a certain period,it will not alter the previous re-signature key.However,the user’s private key does not change,so Sunitha et al.[17] constructed a multi-use PRS scheme with forward security in the e-banking application.Their private key and re-signing key will be updated after a period of time,but their time slice is limited and needs to be set in advance.Although forward-secure schemes have been proposed by some researchers,forward security can only guarantee the security of the key before the leakage,but not after the leakage.Therefore,a key-insulated method in PRS is proposed,which can guarantee both forward and backward security.In addition,while updating the user key,it can also refresh the re-signature key of the proxy,which ensures the security of both user’s signature and re-signature.In general,in order to construct a promising PRS scheme to ensure the unforgeability and non-repudiation in the environment of the EHR,the following properties are generally desired.
1) Unidirectional: When converting the signature,the proxy can only convert in the specified direction.Without authorization,the proxy cannot obtain the reverse conversion key through calculation.
2) Single-use: The Resign algorithm can determine whether the input signature is original or converted.For schemes with single-use property,re-signature cannot be used as the input of this algorithm.
3) Transparent: Nobody could judge the existence of the proxy,and the form of the resignature generated by the proxy is indistinguishable from the signature generated by the user.
4) Non-interactive: In the whole delegating process,there is no need for the delegatee to actually participate,so as to realize the non-interactivity between the delegatee and the delegator.
5) ID-based: The user directly views the public parameter of identity information (ID) as his public key,so there is no need for certificate authority (CA) to specifically produce a certificate to bind the public key with the user.
6) Forward-Secure: The keys generated before the leakage occurred are not correlated with the leaked key,and their security will not be affected.
7) Backward-Secure: Conversely,if after key exposure,the key generated later is still secure,it is called backward security.
1.1 Related Work
The primitive proxy re-signature was first proposed by Blaze et al.[18],but it did not give a specific formal definition so that it did not attract people’s attention for a period of time.Until 2005,Ateniese et al.gave a formal definition and security model for PRS [19].The delegator can authorize the proxy to generate a re-signature key,and then the proxy can utilize this key to convert the designated signature from the delegatee to delegator.Shao et al.[20] eliminated the random model,constructed a PRS scheme under the standard model.Moreover,the PRS scheme in the identity-based cryptosystem was proposed for the first time.Then,Libert et al.[21]solved the open problem left by [19] and proposed the first multi-use unidirectional PRS scheme.The signature can be re-signed by multiple users in sequence,and the direction of conversion is nonreversing.Due to the semi-trusted nature of the proxy,Yang et al.[22] formally proposed the threshold proxy re-signature scheme.Multiple proxies are utilized to jointly perform the resignature process,only when the number of proxies reaches the threshold.In 2011,Shao et al.[23]first combined the unidirectional PRS scheme with the identity-based cryptosystem.In the random oracle,the unforgeability of the signature can be proved based on the extended Computational Diffie-Hellman assumption.In order to save the Computational cost of the verification algorithm,Wang et al.[24] proposed a PRS scheme with server-assisted verification.In this scheme,the proxy can be used to verify the validity of the signature besides resigning,so that the user does not need to undertake the heavy burden of calculation.Then,Patonico et al.[25] put forward an efficient proxy re-signcryption scheme using the arithmetic operation in the elliptic curve,so as to realize the safe ownership transfer in the cloud.Under the attention of quantum computers,in order to resist this kind of attack,some researchers [26,27] turned their direction to construct PRS schemes from the perspective of lattices.Recently,more and more scenarios need to take advantage of the demand for re-signing.The PRS scheme is used in authentication [28–32],auditing [33–37],secure automated valet parking [38] and data sharing [39].
1.2 Contribution
In this paper,we propose the first unidirectional identity-based proxy re-signature scheme with key insulation (KI-IDPRS),which can satisfy all the properties mentioned above.First,an IDbased scheme reduces the overhead of managing public key certificates by taking the user ID as the public key.In addition,considering identity information is fixed for the user,KI-IDPRS can update the private key without changing the public key to achieve the key-insulated property.The proxy can be authorized by the delegator to convert the signature from delegatee into delegator,but not vice versa.What’s more,the secure status of the key at current moment will not affect the keys at other moments,thus realizing key insulation.Although the proxy is semi-trusted,even if both the user and the proxy are compromised at one certain moment,the security is not broken at other times.Security of this scheme can be reduced to extended Computational Diffie-Hellman(eCDH) assumption in the random oracle model.Finally,it can be concluded that our scheme is feasible and has nice properties from the theoretical analysis including experimental results.
1.3 Organization
The following parts of the paper will discuss our proposed scheme as follows: the second part introduces related basic knowledge including system model,the formal definition and security model of the proposed scheme.The third part constructs the first unidirectional identity-based PRS scheme with key insulation and proves the unforgeable security of the proposed scheme.The fourth part puts together other relevant schemes with our scheme from the three dimensions of properties,computing cost and communication overhead,then compares them through experiments.
2 Preliminaries
2.1 Bilinear Map
Given two cyclic groups G,GTof prime orderpandgbe generator of G.A map that meets the following requirements can form a bilinear pairinge:G×G→GT.
1) Bilinearity: ∀x,y∈Z*p,e(gx,gy)=e(g,g)xy.
2) Non-degeneracy:e(g,g)/=1.
3) Computability:e(gx,gy)can be computed.
2.2 eCDH Assumption
In the case of known a tuple<g,ga,gb>∈G,compute the value of a pair(A,Aab),fora,b∈Z*p,A∈G.
2.3 System Model
The proposed scheme requires six entities to complete together: Private key generator (PKG),helper A,helper B,user A in hospital (delegatee),user B in the institution (delegator),and an insurance company (proxy).The system model is depicted in Fig.1,and the description of the notations involved in the model is introduced in Table 1.

Table 1:The list of symbolic representations

Figure 1:System model
PKG: PKG is a trusted authority used to generate secret keys.When a user is supposed to extract its secret key,the identity information will be given to the PKG.The corresponding initial key and helper key will be generated by PKG,and they will be returned to the user and helper,respectively.
Helper A/B: The helper is an auxiliary device with absolute physical security but limited computing power,which is used to store the helper key.It only needs to interact with the user at the beginning of each time period,generate the update key and send it to the user to help the user update the temporary private key,but does not participate in any other cryptographic operations.
User A in hospital: The hospital can act as the delegatee to receive the delegation from the institution,and he sends the signature that needs to be re-signed to the insurance company.
User B in institution: The institution is viewed as the delegator to re-sign user A’s signature into his own signature through the insurance company,rather than directly signing the message.
Insurance company: The insurance company is used to implement the re-signature process through the re-signature key.After receiving the signature of user A and the re-signing key entrusted by user B,he converts the specified signature from A to B.
2.4 Syntax of the KI-IDPRS
A KI-IDPRS scheme consists of eight different algorithms,which are as follows:
1)Setup:This is a system establishment algorithm executed by key generation center (KGC).Security parameter 1kis given to KGC and the master public keympkis returned back for public use,the master secret keymskis returned for PKG.
2)Extract:This is an initial private key extraction algorithm executed by PKG.The master secret keymskand a user’s identityIDare the input of PKG.Then,PKG outputs the initial private keySKID,0stored by the user and the helper keyHKIDstored by the helper for the identityID.
3)HUpdate:This is an update key generation algorithm executed by the helper.The helper keyHKIDfor the identityIDand the time periodj,iare as the input of the helper.Then,the helper outputs the update keyHKUID,j→iused to update time period j to i.
4)UUpdate:This is a temporary private key update algorithm executed by the user.The private keySKID,jin the old time periodjfor the identityIDand the update keyHKUID,j→iare as the input of the user.Then,the user outputs the private keySKID,iin the new time periodifor the identityID.
5)RKGen:This is a re-signature key generation algorithm executed by the delegator.The delegatee’s identityIDAand the delegator’s private keySKIDB,iin the time periodiare as the input of the delegator.Then,the delegator outputs the re-signature keyRKA→B,ito the proxy,which is used to implement signature conversion from identityIDAtoIDBunder the same messagemin the time periodi.
6)Sign:This is a signature generation algorithm executed by the user/delegatee.The private keySKIDA,iin the time periodifor the identityIDA,messagemand the signature’s levelLare as the input of the delegatee.Then,the delegatee outputs signature,i)at levelLin the time periodi,whereL=1,2.
7)ReSign:This is a re-signature conversion algorithm executed by the proxy.The original signature,i)at level 1,messagem,the delegatee’s identityIDAand the re-signature keyRKA→B,iare as the input of the proxy.Then,the proxy outputs the signature,i)at level 2 for identityIDBin the time periodi,if,i)can pass theVerifyalgorithm.
8)Verify:This is a verification algorithm.The alleged signature,i)at levelL,messagemand the identityIDare as the input.Then,1 can be returned if the signature is valid.
2.5 Security Model of the KI-IDPRS
To assess the security of the key-insulated proxy re-signature in a formal manner,the following interactive game between the challengerCand the adversaryAis defined by incorporating the security model for the key insulated signature [40] and the one for the proxy re-signature [23].
Setup: Cperforms the algorithm Setup to generate the master public keympkand the master secret keymsk,and then returnsmpktoAwhile keepsmsksecret.
Query:Before the adversaryAattempts to forge a signature,the challengerCpermits him to adaptively make a number of different queries.
O(Extract):Cperforms the algorithm Extract to produce the userID′sinitial secret keySKID,0forA’s request(ID).
O(UUpdate):Cperforms the algorithm UUpdate to produce the userID′stemporary secret keySKID,iin time periodiforA’s request(ID,i).
O(RKGen):Cperforms the algorithm RKGen to produce the re-signature keyRKA→B,iin time periodiforA’s request(IDA,IDB,i).
O(Sign):Cperforms the algorithm Sign to produce the signature(σ,L,i)in time periodiforA’s request(ID,L,i,m).
O(ReSign):Cperforms the algorithm ReSign to produce the re-signature(σ′,L+1,i)in time periodiforA’s request(σ,L,i,m,IDA,IDB).
Forgery Output:Suppose(ID*,m*,σ*,L*,i*)isA’s counterfeit result after queries.If the adversary meets the following restrictions at the same time,and can still generate a valid signature that makes the equation Verify(σ,i,m,ID)=1 hold,then the adversary is considered to be the winner in this game.
1)Acan’t queryID*inO(Extract)
2)Acan’t query(ID*,i*)inO(UUpdate)
3)Acan’t queryID*inO(RKGen)
4)Acan’t query(ID*,m*,i*,L*)inO(Sign)
5)Acan’t query(σ*IDj,i*,m*,IDj,ID*)inO(ReSign)
3 Our Proposed KI-IDPRS Scheme
3.1 Construction
By combining identity-based key-insulated signature [41] in the unidirectional IDPRS [23],the concrete construction of the unidirectional identity-based PRS scheme with insulated key has been given as follows:
· Setup(1k)→(mpk,msk): After giving the security parameter 1k,the following operations are performed by KGC to generate the public keympkand the master secret keymsk.
1) Choose two finite cyclic groups G,GTwith prime orderand choose a generatorgof G.
2) Pick bilinear pairinge:G×G→GT;
3) Generate the master key:Z*pand computeX=gx;
4) Define three hash functions:H1(·),H2(·):{0,1}*→Z*p,H3(·):{0,1}*→G;
5) Generate the public key(mpk=(g,p,G,GT,e,X,H1,H2),msk=x).
· Extract(ID,msk)→(HKID,SKID,0): After inputting the master secret keymskand a user’s identityID,PKG firstiy randomly chooses one elementHKID R←-Z*pas the helper key.Then,it computes the initial secret keymodp,and setsIn fact,for a user,hiscan be obtained by other users,onlyis kept private.Because it is obvious to find that the user’s signature hasas one of the components,andis not updated in our proposed scheme.
· HUpdate(HKID,ID,i,j)→HKUID,j→i: On receiving the helper keyHKIDforIDand the time periodj,i,the helper outputs the update keyHKUID,j→iby computingHKUID,j→i=HKID·(H2(ID‖i)-H2(ID‖j)).
· UUpdate(SKID,j,HKUID,j→i,ID,i,j)→SKID,i: After receiving the private keySKID,jin the old time periodjand the update keyHKUID,j→i,the user updates the private keySKID,ias follows:

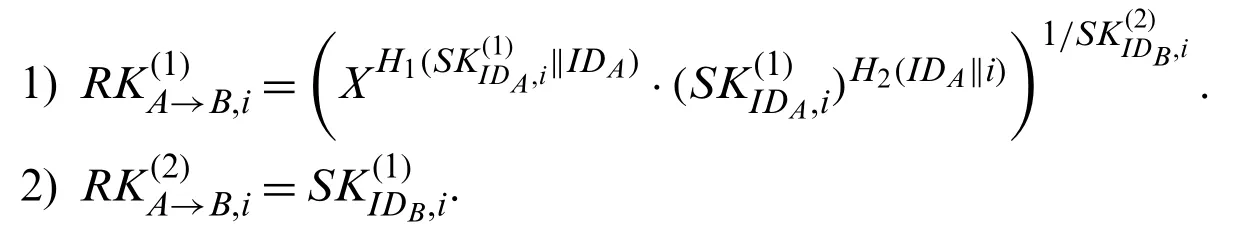
· RKGen(IDA,SKIDB,i)→RKA→B,i: After the delegator receives the identityIDAof the delegatee,the delegator calculatesRKA→B,ithrough its private keySKIDB,ias follows and then gives it to the proxy.
· Sign(ID,m,SKID,i)→After receiving the message,the delegatee signs the messagemwithIDAand the private keySKIDA,i.First-level signatureand secondlevel signatureare computed as follows,and then the first-level signatureis given to the proxy to generate the re-signature of the delegator.

· ReSign,RKA→B,i)→: After receiving the delegatee’s first-level signatureand the re-signature keyRKA→B,i,the proxy first ensures the legality of the signatureby examining whether the equationcan be satisfied.If not,an error is output.Otherwise,the proxy calculates the second-level signatureof the delegator as follows:

· Verify(σ,i,m,ID)→1/⊥: After entering the signatureσ[1]/σ[2],messagem,and identityID,the algorithm checks the validity of the first-level signature through equation=e(σ(1),g),and the validity of the second-level signature through equation
3.2 Security Analysis
In the random oracle model,our proposal is existentially unforgeable under the eCDH assumption in G.
共7个参试品种,分别是轮选166、泉麦29、郑麦1860、周麦18、农大2011、珍麦3号、泰禾麦2号,对照为周麦18。
Proof: Assume that there is an adversaryAcan break the existential unforgeability of our proposal with non-negligible probabilityε,then we can build another algorithmBto solve the eCDH problem.The input of eCDH problem is(g,ga,gb),and the goal of security proof is to get(A,Aab),where A could be any element in G.
Setup: The challengerCinitializes the system according to the following steps:
1) SetX=ga;
2) Sendmpk=(g,p,G,GT,e,X,H1,H2,H3)toA,where the values ofH1,H2andH3can be obtained through the followingO(H1),O(H2)andO(H3)queries,respectively.
Query:
·O(H1)→(R||ID,h1)∈
1)Ainputs(R||ID)to query the value ofH1(R||ID);
2) If there is the item(R||ID)in the,Creturns the correspondingh1toA;
3) If not,Crandomly chooses one elementh1from Z*pas output and adds it to the.
·O(H2)→(ID||i,h2)∈
1)Ainputs(ID||i)to query the value ofH2(ID||i);
2) If there is the item(ID||i)in theHlist2,Creturns the correspondingh2toA;
3) If not,Crandomly chooses one elementh2from Z*pas output and adds it to the.
·O(H3)→(m,α,(gb)α)∈
1)Ainputsmto query the value ofH3(m);
2) Ifmcan be found in,Creturns the correspondingh3=(gb)αtoA;
3) If not,Arandomly chooses one elementαfrom Z*pand computes(gb)αas output,then adds it to the.
·O(Extract)→(ID,SKID,0)
1)AinputsIDto query the corresponding initial secret keySKID,0;
2)Crandomly choosesand computes
4) If not,Caddsto theand returnsas the initial secret key toA.
·O(UUpdate)→(ID,i,SKID,i)
1)AinputsIDand the time periodito query the temporary secret keySKID,0in the time periodi;
2)Crandomly choosesand computes
4) If not,Caddsto theand returnsas the temporary secret key for time perioditoA.
·O(RKGen),O(Sign),O(ReSign)
1)Aobtains the corresponding private key viaO(Extract)andO(UUpdate);
2)Ccomputes the required query value via the corresponding private key and returns it toA;
Forgery Output:
According to the forking lemma [42],for level 1,Acan counterfeit two valid signaturesh1andh′1are two different random responses fromO(H1)on inputthenBcan compute:
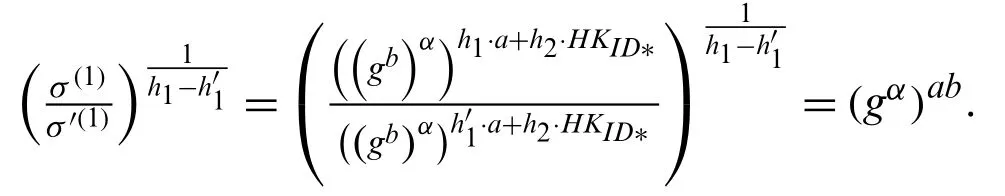
Similarly,for level 2,Acan counterfeit two valid signaturesThen,Bcan compute:

4 Comparison
Comparison between our KI-IDPRS scheme and state-of-the-art [21,30,43] will be comprehensively discussed from the perspective of properties,computation cost,and communication overhead.The schemes involved in the comparison are the first PRS scheme featured with the multi-use and unidirectional translation [21],the PRS scheme with key-leakage resistance [43]and the up-to-dated PRS scheme [30].Then,the simulated implementation of these schemes is conducted through the experimental platform.
4.1 Simulated Implementation
To make the following theoretical analysis more convincing,these schemes are simulated on a specific experimental platform.The computer’s operating system is 64-bits Windows 10,the processor is Intel Core i7-7700 @ 3.60 GHz,and the memory is 8GB.Based on VC++6.0,cryptography operations are implemented with the Pairing-Based Cryptography (PBC) library [44],where parameter is the standard parametera.paramand |G|=128 bytes,=20 bytes.In addition,the unit time of critical operations is separately measured and listed in Table 2.
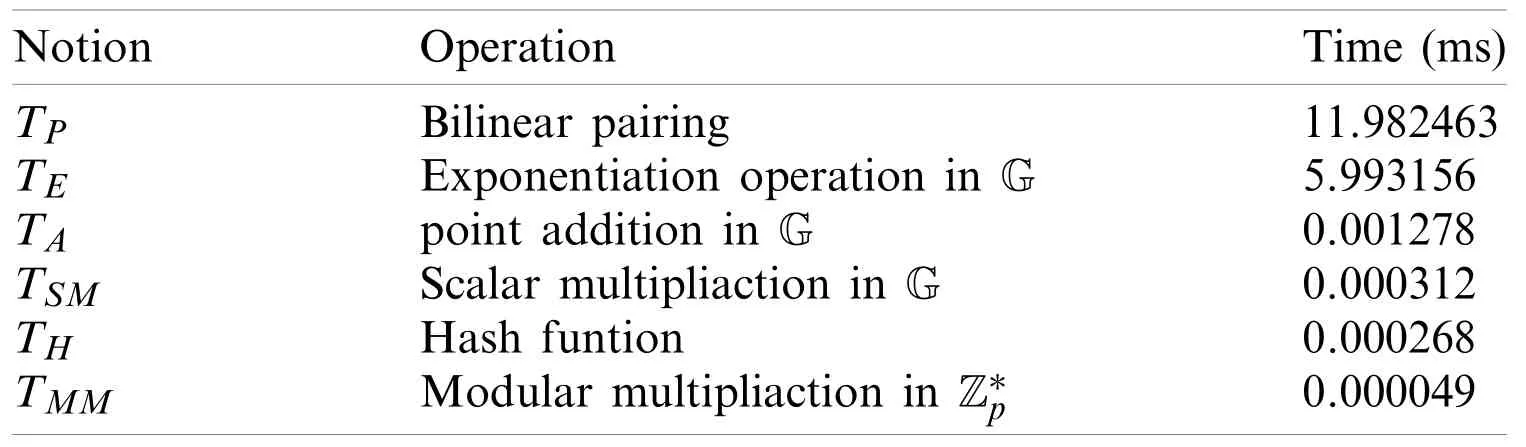
Table 2:The time costs of cryptographic operations
4.2 Properties
We list the properties of the proposed scheme and the relevant work [21,30,43] in Table 3,wheremeans that the property is supported,“×” means that the feature is not supported.According to the comparison results,it is obvious that all the desired properties can be satisfied in our protocol.Although the scheme [21] owns several desired properties of PRS,this scheme is built in the public key infrastructure and is difficult to be deployed in practical in view of the burden brought by the public-key certificates.In scheme [43],the identity-based cryptographic system is applied to simplify certificate management.Besides,the schemes [30,43] have forward security to prevent the key leakage from affecting the previous key.However,they ignore the security of the private key after key exposure.Only our scheme could provide the key insulated property and thus achieve forward and backward security simultaneously.Although schemes [43]and [30] realize forward security,they divide the time into a presetting limited time period for updating private keys.In contrast to the works in [30,43],the proposed scheme provides unlimited periods.

Table 3:The properties comparison in different schemes
4.3 Communication Overhead
The communication overhead of these schemes is discussed in Table 4,Figs.2 and 3,where|G|andrepresent the length of an element in group G and group Z*p,respectively.In the experiment,we take |G|=128 bytes and=20 bytes.Scheme [21],[30] and our signature length are both 2|G|,and scheme [43] is the longest.In addition,the length of the re-signature is the same.In terms of the re-signature key,our size is one more |G|than scheme [21] and one |G|less than schemes [43] and [30].In general,the length of signature and re-signature in KI-IDPRS is less than or equal to other schemes.Therefore,the proposed scheme does not occupy more communication overhead compared with other schemes.

Table 4:The comparison of computation costs
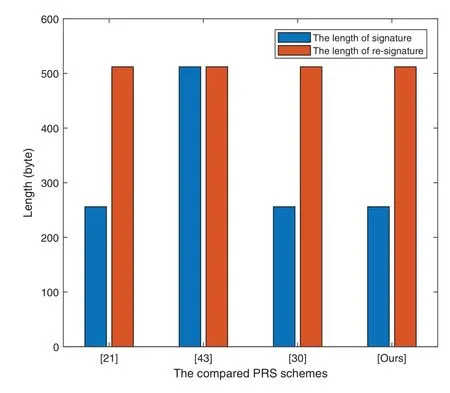
Figure 2:Comparison of signature/re-signature size
4.4 Computation Cost
From the data in Table 2,it is clear that the hash function,scalar multiplication,and modular multiplication take relatively little time.Therefore,exponential and pairing operations are mainly considered in the theoretical analysis of these schemes.TEis used to represent the time required to perform an exponential operation in group G,andTPrepresents the runtime of a bilinear pairing.In the signature phase,results in Table 5,Figs.4–6 can illustrate that our scheme is less than or equal to other schemes in terms of computational overhead.In the process of re-signing,the scheme [21] requires six exponential operations,which is more than our scheme.However,the schemes [43] and [30] only require two and three exponential operations,respectively.Our KI-PRS scheme requires five,which is acceptable,because our scheme can support both forward and backward security.When checking the validity of the first-level signature,it only takes more time than the scheme [30],whereTP≈2TE.When performing the verification of second-level signature,our scheme requires four exponential operations and two pairing operations (that is,approximately equal to fiveTP),which is no more than other schemes.In short,compared with other schemes,KI-IDPRS may not cost more time than some schemes,but this is acceptable for the acquisition of functional and safety enhancements.

Table 5:The comparison of computation costs

Figure 3:Comparison of re-signature key/private key size
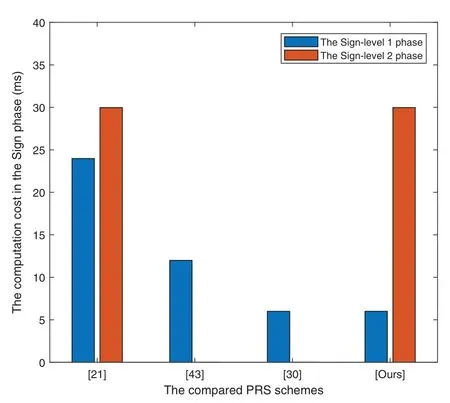
Figure 4:Comparison of sign phase time

Figure 5:Comparison of verify phase time

Figure 6:Comparison of ReSign phase time
5 Conclusion
This paper proposes the first KI-IDPRS scheme,which is conducive to timely dealing with the occurrence of key leakage in the EHR sharing system.Then,the formal definition and the security model of KI-IDPRS are given.On this basis,a concrete KI-IDPRS scheme is constructed and proved to have unforgeable security under the eCDH assumption in the random oracle model.What’s more,the presented KI-IDPRS scheme can support both forward and backward security,updating private key within unlimited periods.Accordingly,key leakage will not cause a catastrophic threat to the EHR sharing system.Finally,from theoretical analysis and experiment evaluation,related schemes are compared from three dimensions in properties,communication and computation costs.The presented KI-IDPRS is the only scheme with all the promising properties.
Funding Statement: This work is partially supported by the Network and Data Security Key Laboratory of Sichuan Province under the Grant No.NDS2021-2,in part by Science and Technology Project of Educational Commission of Jiangxi Province under the Grant No.GJJ190464,and in part by National Natural Science Foundation of China under the Grant No.71661012.
Conflicts of Interest: The authors declare that they have no conflicts of interest to report regarding the present study.
杂志排行
Computer Modeling In Engineering&Sciences的其它文章
- Analysis of Multi-AGVs Management System and Key Issues:A Review
- Assessment of the Solid Waste Disposal Method during COVID-19 Period Using the ELECTRE III Method in an Interval-Valued q-Rung Orthopair Fuzzy Approach
- Sentiment Analysis of Roman Urdu on E-Commerce Reviews Using Machine Learning
- Nonlinear Response of Tunnel Portal under Earthquake Waves with Different Vibration Directions
- A Method Based on Knowledge Distillation for Fish School Stress State Recognition in Intensive Aquaculture
- Detecting and Repairing Data-Flow Errors in WFD-net Systems
